将Lambda函数写入S3 - IAM策略以访问S3。
将Lambda函数写入S3 - IAM策略以访问S3。
提问于 2019-07-09 08:34:00
下面是我的策略,它授予读写访问仍然不能写入S3桶的权限。
问题
仍然出现以下错误:
未能将/tmp/test.txt上载到桶名/Automation_2019-07-09 04:20:32_.csv:调用PutObject操作:拒绝访问时出错(AccessDenied)
策略
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "ConsoleAccess",
"Effect": "Allow",
"Action": [
"s3:GetAccountPublicAccessBlock",
"s3:GetBucketAcl",
"s3:GetBucketLocation",
"s3:GetBucketPolicyStatus",
"s3:GetBucketPublicAccessBlock",
"s3:ListAllMyBuckets"
],
"Resource": "*"
},
{
"Sid": "ListObjectsInBucket",
"Effect": "Allow",
"Action": "s3:ListBucket",
"Resource": [
"arn:aws:s3:::bucketname"
]
},
{
"Sid": "AllObjectActions",
"Effect": "Allow",
"Action": "s3:*Object",
"Resource": [
"arn:aws:s3:::bucketname/*"
]
}
]
}桶政策
{
"Version": "2012-10-17",
"Id": "MYBUCKETPOLICY",
"Statement": [
{
"Sid": "DenyIncorrectEncryptionHeader",
"Effect": "Deny",
"Principal": "*",
"Action": "s3:PutObject",
"Resource": "arn:aws:s3:::bucket-name/*",
"Condition": {
"StringNotEquals": {
"s3:x-amz-server-side-encryption": "aws:kms"
}
}
},
{
"Sid": "DenyUnEncryptedObjectUploads",
"Effect": "Deny",
"Principal": "*",
"Action": "s3:PutObject",
"Resource": "arn:aws:s3:::bucket-name/*",
"Condition": {
"Null": {
"s3:x-amz-server-side-encryption": "true"
}
}
}
]
}Python代码(在Lambda函数中)相关部分代码
s3 = boto3.resource('s3', config=Config(signature_version='s3v4'))
target_bucket = 'bucket-name'
target_file = "Output/Automation_Result_"+EST+"_.txt"
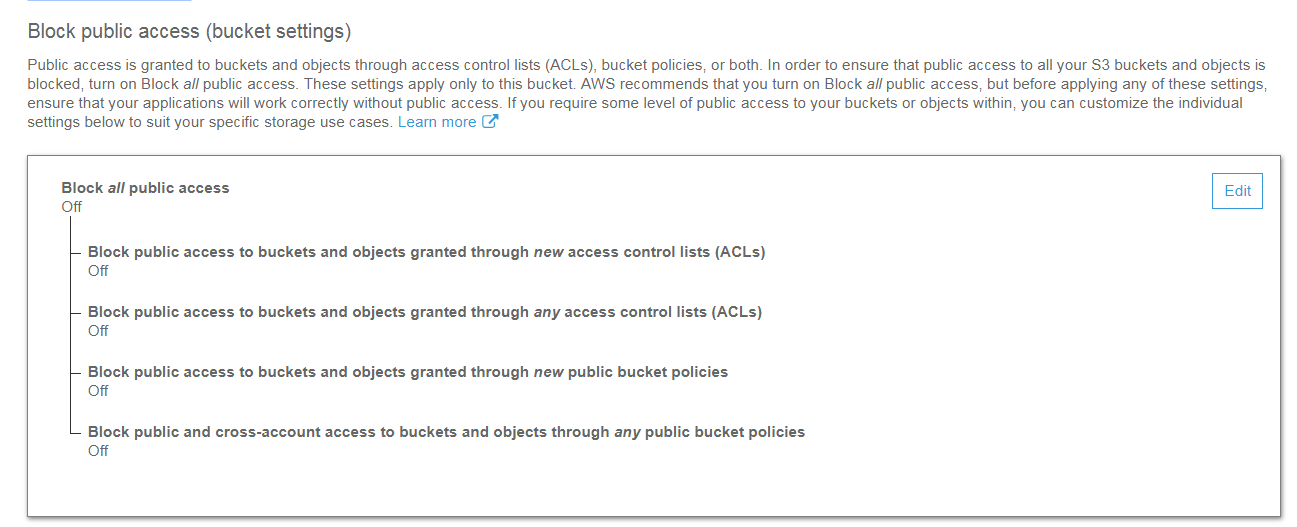
s3.meta.client.upload_file('/tmp/test.txt', target_bucket, target_file, ExtraArgs={"ServerSideEncryption": "aws:kms", "SSEKMSKeyId":"XXXXXXX-XXXX-XXXX" })这就是我的桶式公共访问的样子!
回答 1
Stack Overflow用户
发布于 2019-07-09 12:37:57
对我来说很好!
我将您的策略重命名为桶,并将其附加到一个用户,作为他们的唯一策略。
然后,我能够成功地将一个对象从复制到桶中,并从桶中复制对象。
如果它不适用于您,则要么您不使用与此策略关联的凭据,要么有另一个策略阻止访问,例如拒绝策略或范围限制策略。
页面原文内容由Stack Overflow提供。腾讯云小微IT领域专用引擎提供翻译支持
原文链接:
https://stackoverflow.com/questions/56948464
复制相关文章
相似问题

