尽管防火墙规则,但无法连接到实例上的端口80
总之,虽然我已经设置了允许tcp:80的防火墙规则,但位于“默认”网络上的GCE实例不接受与端口80的连接。在我的实例中,似乎只有端口22是打开的。我可以点击它,但不能在64跳以下追踪到它。
以下是我的调查,使我得出了这些结论。
gcloud beta compute firewall-rules list
NAME NETWORK DIRECTION PRIORITY ALLOW DENY
default-allow-http default INGRESS 1000 tcp:80
default-allow-https default INGRESS 1000 tcp:443
default-allow-icmp default INGRESS 65534 icmp
default-allow-internal default INGRESS 65534 tcp:0-65535,udp:0-65535,icmp
default-allow-rdp default INGRESS 65534 tcp:3389
default-allow-ssh default INGRESS 65534 tcp:22
temp default INGRESS 1000 tcp:8888
gcloud compute instances list
NAME ZONE MACHINE_TYPE PREEMPTIBLE INTERNAL_IP EXTERNAL_IP STATUS
ssrf3 us-west1-c f1-micro true 10.138.0.4 35.197.33.182 RUNNING
gcloud compute instances describe ssrf3
...
name: ssrf3
networkInterfaces:
- accessConfigs:
- kind: compute#accessConfig
name: external-nat
natIP: 35.197.33.182
type: ONE_TO_ONE_NAT
kind: compute#networkInterface
name: nic0
network: https://www.googleapis.com/compute/v1/projects/hack-170416/global/networks/default
networkIP: 10.138.0.4
subnetwork: https://www.googleapis.com/compute/v1/projects/hack-170416/regions/us-west1/subnetworks/default
...
tags:
fingerprint: 6smc4R4d39I=
items:
- http-server
- https-server我进入35.197.33.182 (这是ssrf3实例)并运行:
sudo nc -l -vv -p 80在我的本地机器上,我运行:
nc 35.197.33.182 80 -vv
hey但什么都没发生。所以我试着给主人打电话。这看起来很健康:
ping 35.197.33.182
PING 35.197.33.182 (35.197.33.182): 56 data bytes
64 bytes from 35.197.33.182: icmp_seq=0 ttl=57 time=69.172 ms
64 bytes from 35.197.33.182: icmp_seq=1 ttl=57 time=21.509 msTraceroute在64次跳跃后退出,但未到达35.197.33.182号目的地。
所以我用nmap检查哪些端口是打开的:
nmap 35.197.33.182
Starting Nmap 7.12 ( https://nmap.org ) at 2017-06-18 16:39 PDT
Note: Host seems down. If it is really up, but blocking our ping probes, try -Pn
Nmap done: 1 IP address (0 hosts up) scanned in 3.06 seconds
nmap 35.197.33.182 -Pn
Starting Nmap 7.12 ( https://nmap.org ) at 2017-06-18 16:39 PDT
Nmap scan report for 182.33.197.35.bc.googleusercontent.com (35.197.33.182)
Host is up (0.022s latency).
Not shown: 999 filtered ports
PORT STATE SERVICE
22/tcp open ssh
Nmap done: 1 IP address (1 host up) scanned in 6.84 seconds…即使我运行的是35.197.33.182的nc -l -p 80。
回答 4
Stack Overflow用户
发布于 2017-06-19 10:04:38
确保VM级防火墙没有介入。例如,与所有其他默认映像相比,容器优化的OS有点特殊:
默认情况下,容器优化的OS主机防火墙只允许传出连接,并且只接受通过SSH服务传入的连接。若要接受容器优化OS实例上的传入连接,必须打开您的服务正在侦听的端口。
https://cloud.google.com/container-optimized-os/docs/how-to/firewall
Stack Overflow用户
发布于 2019-07-05 16:31:37
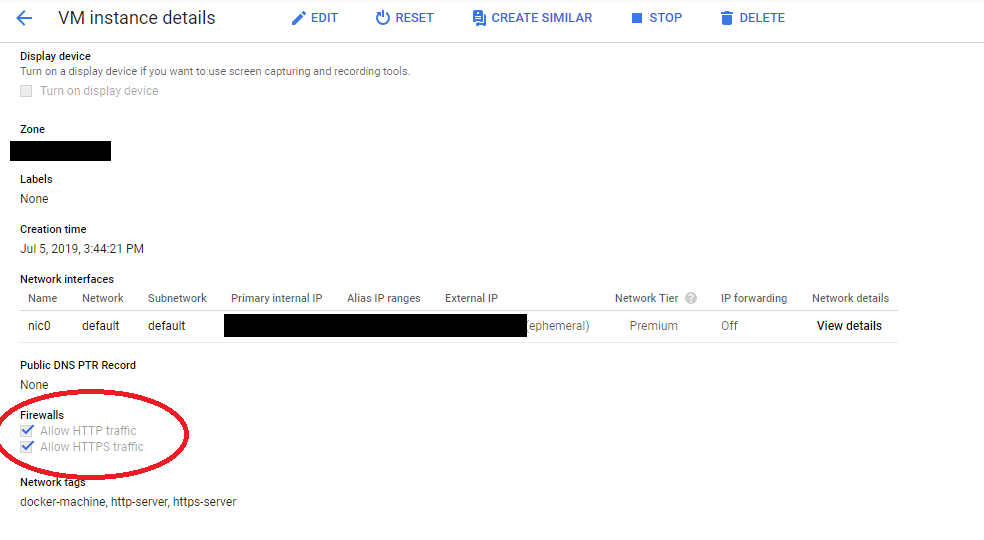
选中“允许HTTP流量”和“允许HTTPS流量”这两个复选框就成功了。这创建了两个防火墙规则,打开端口80和443。由于某些原因,手动添加这些端口的规则不起作用,但是它可以检查这些框。
Stack Overflow用户
发布于 2019-10-30 20:13:00
经过大量的跟踪和错误之后,下面的程序在ubuntu-1404-trusty-v20190514上为我工作,一个nodejs应用程序监听端口8080。接受端口80和8080,然后重定向80到8080.
sudo iptables -A INPUT -i eth0 -p tcp --dport 80 -j ACCEPT
sudo iptables -A INPUT -i eth0 -p tcp --dport 8080 -j ACCEPT
sudo iptables -t nat -A OUTPUT -o lo -p tcp --dport 80 -j REDIRECT --to-port 8080
sudo iptables -A PREROUTING -t nat -i eth0 -p tcp --dport 80 -j REDIRECT --to-port 8080https://stackoverflow.com/questions/44620723
复制相似问题

