从EC2访问运动的问题
从EC2访问运动的问题
提问于 2017-06-02 17:39:44
我有一些java代码,可以从Kinesis中提取记录。它在我的笔记本电脑上运行很好(不管是什么IP),但是当我试图在EC2上运行它时,我会得到以下错误:
Exception in thread "main" com.amazonaws.SdkClientException: Unable to load AWS credentials from any provider in the chain
at com.amazonaws.auth.AWSCredentialsProviderChain.getCredentials(AWSCredentialsProviderChain.java:131)
at com.amazonaws.http.AmazonHttpClient$RequestExecutor.getCredentialsFromContext(AmazonHttpClient.java:1119)
at com.amazonaws.http.AmazonHttpClient$RequestExecutor.runBeforeRequestHandlers(AmazonHttpClient.java:759)
at com.amazonaws.http.AmazonHttpClient$RequestExecutor.doExecute(AmazonHttpClient.java:723)
at com.amazonaws.http.AmazonHttpClient$RequestExecutor.executeWithTimer(AmazonHttpClient.java:716)
at com.amazonaws.http.AmazonHttpClient$RequestExecutor.execute(AmazonHttpClient.java:699)
at com.amazonaws.http.AmazonHttpClient$RequestExecutor.access$500(AmazonHttpClient.java:667)
at com.amazonaws.http.AmazonHttpClient$RequestExecutionBuilderImpl.execute(AmazonHttpClient.java:649)
at com.amazonaws.http.AmazonHttpClient.execute(AmazonHttpClient.java:513)
at com.amazonaws.services.securitytoken.AWSSecurityTokenServiceClient.doInvoke(AWSSecurityTokenServiceClient.java:1271)
at com.amazonaws.services.securitytoken.AWSSecurityTokenServiceClient.invoke(AWSSecurityTokenServiceClient.java:1247)
at com.amazonaws.services.securitytoken.AWSSecurityTokenServiceClient.executeAssumeRole(AWSSecurityTokenServiceClient.java:454)
at com.amazonaws.services.securitytoken.AWSSecurityTokenServiceClient.assumeRole(AWSSecurityTokenServiceClient.java:431)有问题的代码似乎让它不开心:
AWSSecurityTokenServiceClient sts = new AWSSecurityTokenServiceClient();
AssumeRoleResult assumeRoleResult = sts.assumeRole(new AssumeRoleRequest()
.withRoleArn(config.getString("kinesis/arn"))
.withExternalId(config.getString("kinesis/external_id"))
.withRoleSessionName(config.getString("kinesis/role_session_name")));我想知道这是否与如何构建EC2实例有关。但是,它在我的调试器上运行得很好,这让我感到困惑。
我已经检查过,以确保各种配置值是正确通过的。
Per@prayagupd更新了EC2实例以包含以下策略:
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"kinesis:Get*",
"kinesis:List*",
"kinesis:Describe*"
],
"Resource": "*"
}
]
}现在的错误是:
Exception in thread "main" com.amazonaws.services.securitytoken.model.AWSSecurityTokenServiceException:
User: arn:aws:sts::12345:assumed-role/kinesis-consumer/i-cab01a5
is not authorized to perform:
sts:AssumeRole on resource: arn:aws:iam::12345:role/kinesis-consumer 回答 1
Stack Overflow用户
发布于 2017-06-02 17:50:45
从您的ec2,您需要通过您的ec2 VM配置文件进行身份验证。
我使用下面的代码,它连接到使用(~/.aws/credentials)的属性(~/.aws/credentials)中的属性~/.aws/credentials,对我来说~/.aws/credentials是临时的。
因此,我在ec2中使用了ec2,它实际上是查找ec2实例配置文件。
您仍然可以将您的凭据放在~/.aws/credentials中并使用它。
/**
* provides credentials for a client to make connection to the elastic cloud instance
*
* @return DefaultAWSCredentialsProviderChain
*/
private DefaultAWSCredentialsProviderChain getAuthProfileCredentials() {
if (myAppConfig.getProperty("authentication.profile") != null) {
System.setProperty(AwsProfileNameLoader.AWS_PROFILE_SYSTEM_PROPERTY, myAppConfig.getProperty("authentication.profile"));
}
return new DefaultAWSCredentialsProviderChain();
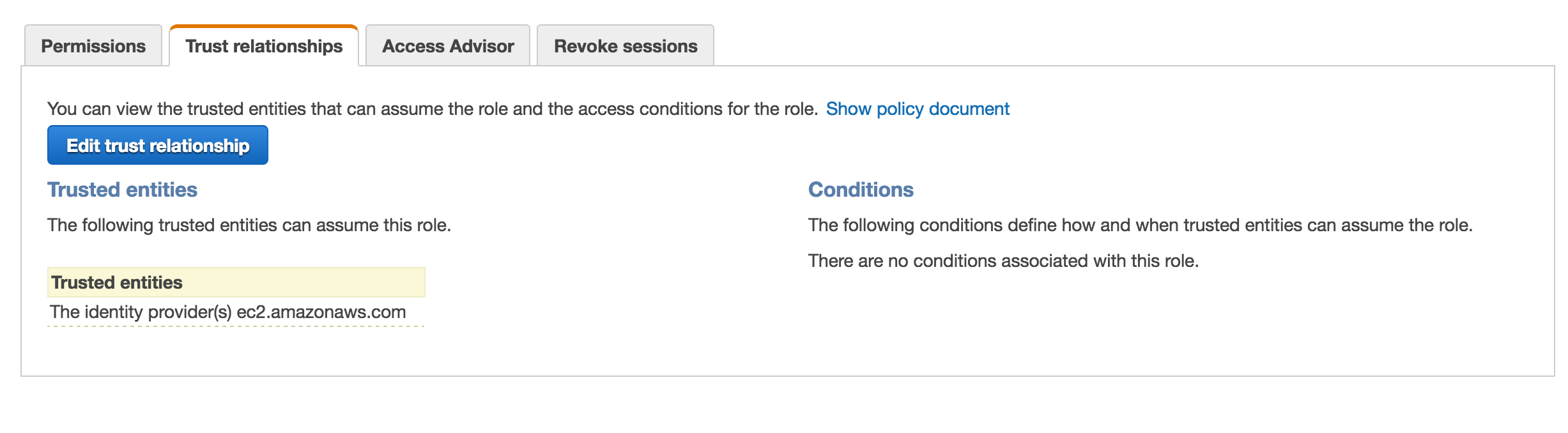
}您的ec2实例配置文件需要具有以下信任关系的动态访问IAM角色。
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Principal": {
"Service": "ec2.amazonaws.com"
},
"Action": "sts:AssumeRole"
}
]
}
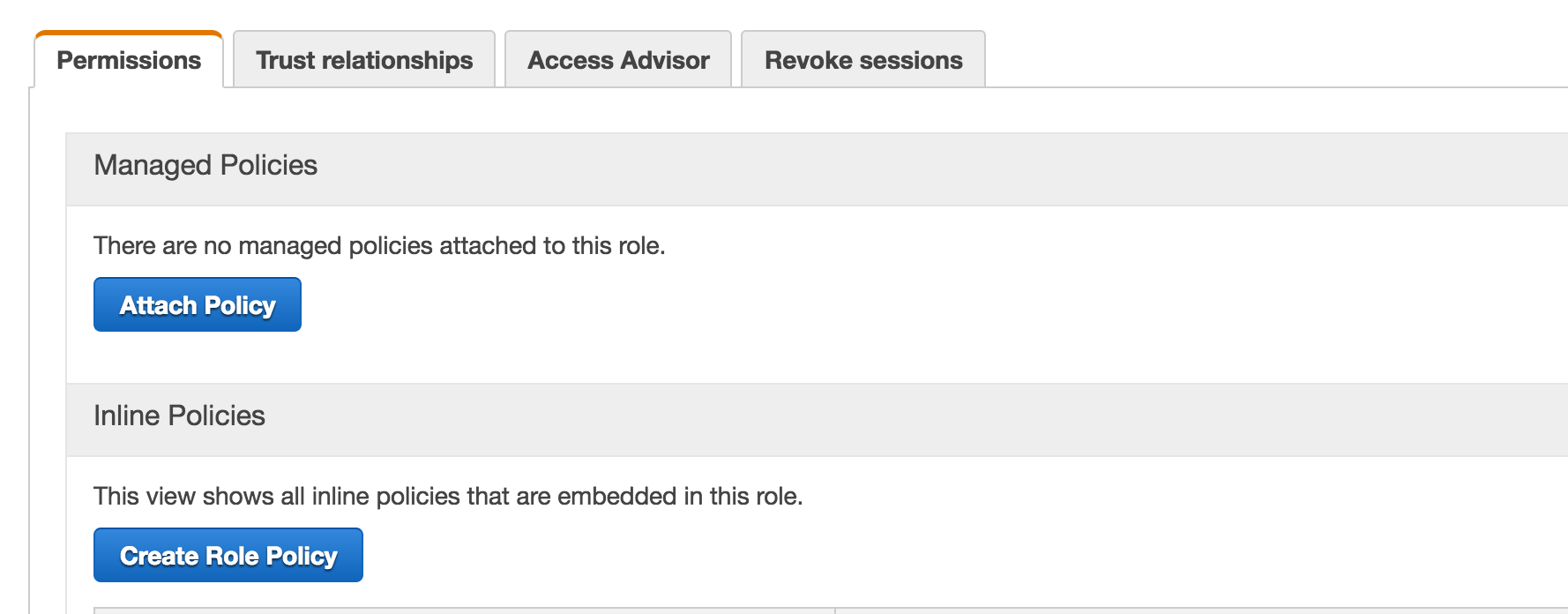
角色政策应该有
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"kinesis:*"
],
"Resource": [
"arn:aws:kinesis:us-west-2:*:stream/*"
]
}
]
}
然后,可以在ec2机器上使用以下命令来验证动态访问(aws cli应该已经安装)
aws kinesis create-stream --stream-name gregor-samsa-ping --shard-count 1 --region us-west-2
aws kinesis list-streams --region us-west-2
{
"StreamNames": [
"gregor-samsa-ping"
]
}页面原文内容由Stack Overflow提供。腾讯云小微IT领域专用引擎提供翻译支持
原文链接:
https://stackoverflow.com/questions/44334590
复制相关文章
相似问题

