使用itsdangerous.BadSignature - App后端服务器进行令牌集成中的TimedJSONWebSerializer错误?
使用itsdangerous.BadSignature - App后端服务器进行令牌集成中的TimedJSONWebSerializer错误?
提问于 2016-07-02 00:16:47
我是通过一个只知道后端和客户端的secret_key对用户进行身份验证,并在Postman中通过标头。到目前为止,我的代码如下:
from itsdangerous import TimedJSONWebSignatureSerializer
from constants import SECRET_KEY
@app.route('/authUser', methods=['POST'])
def authUser():
secret_key = request.headers['secret_key']
if secret_key is None:
return "400"
elif secret_key != SECRET_KEY: # SECRET_KEY is a constant that has been imported from constants.py
return "400"
else:
s = TimedJSONWebSignatureSerializer(app.config['SECRET_KEY'], expires_in=3600)
token = s.dumps({'user_id' : user_id})
print (s.loads(token))
return token此代码引发以下错误:
Traceback (most recent call last):
File "C:/Users/vaibhav/PycharmProjects/Coding/Coding.py", line 15, in <module>
print (s.loads(token))
File "C:\Users\vaibhav\Anaconda\lib\site-packages\itsdangerous.py", line 798, in loads
self, s, salt, return_header=True)
File "C:\Users\vaibhav\Anaconda\lib\site-packages\itsdangerous.py", line 752, in loads
self.make_signer(salt, self.algorithm).unsign(want_bytes(s)),
File "C:\Users\vaibhav\Anaconda\lib\site-packages\itsdangerous.py", line 377, in unsign
payload=value)
itsdangerous.BadSignature: Signature 'Ch8y6BDMIIBdIGM0lmjdAimINvP3PnUmBpOp-jDW18w' does not match如果我改变了行文:
s = TimedJSONWebSignatureSerializer(app.config['SECRET-KEY'], expires_in=3600)对此:
s = TimedJSONWebSignatureSerializer('SECRET-KEY', expires_in=3600)代码工作正常,没有问题。
QUETSION :请告诉我为什么会像配置处理那样工作,app.config('SECRET-KEY')也会返回一个秘密密钥。
为了学习令牌身份验证,我参考了这个网站:
用烧瓶进行RESTful认证
提前感谢!
回答 1
Stack Overflow用户
回答已采纳
发布于 2016-08-02 06:29:19
你能不能先确定你设置了密匙,比如
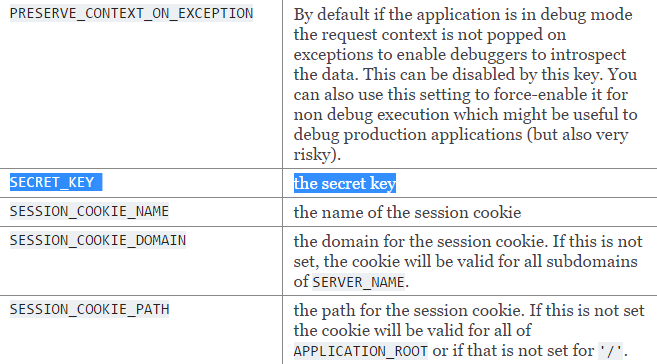
app.secret_key = 'whatever the secret is'这将初始化秘密。
页面原文内容由Stack Overflow提供。腾讯云小微IT领域专用引擎提供翻译支持
原文链接:
https://stackoverflow.com/questions/38155288
复制相关文章
相似问题

