spnego和kerberos在gss中的应用
spnego和kerberos在gss中的应用
提问于 2021-05-21 19:11:31
我试图重用一些现有的代码,在一个新的Quarkus应用程序中启用spnego身份验证。当作为标准JAR编译并与OpenJDK 11一起运行时,Quarkus应用程序工作得很好。一旦我将其打包为本地可执行文件(在linux上),我就会得到以下异常:
2021-05-21 17:31:17,178 ERROR [com.organisation.sec.ker.eng.gss.AbstractGssAuthenticator] (executor-thread-1) GSS error occured: GSSException: Failure unspecified at GSS-API level (Mechanism level: Invalid argument (400) - Cannot find key of appropriate type to decrypt AP-REQ - RC4 with HMAC)
at sun.security.jgss.krb5.Krb5Context.acceptSecContext(Krb5Context.java:859)
at sun.security.jgss.GSSContextImpl.acceptSecContext(GSSContextImpl.java:361)
at sun.security.jgss.GSSContextImpl.acceptSecContext(GSSContextImpl.java:303)
at sun.security.jgss.spnego.SpNegoContext.GSS_acceptSecContext(SpNegoContext.java:905)
at sun.security.jgss.spnego.SpNegoContext.acceptSecContext(SpNegoContext.java:556)
at sun.security.jgss.GSSContextImpl.acceptSecContext(GSSContextImpl.java:361)
at sun.security.jgss.GSSContextImpl.acceptSecContext(GSSContextImpl.java:303)
at com.organisation.security.kerberos.engine.gss.AbstractGssAuthenticator$AuthAction.run(AbstractGssAuthenticator.java:110)
at com.organisation.security.kerberos.engine.gss.AbstractGssAuthenticator$AuthAction.run(AbstractGssAuthenticator.java:77)
at java.security.AccessController.doPrivileged(AccessController.java:147)
at javax.security.auth.Subject.doAs(Subject.java:423)
at com.organisation.security.kerberos.engine.gss.AbstractGssAuthenticator.handle(AbstractGssAuthenticator.java:49)
at com.organisation.security.kerberos.KerberosAuthenticationFilter.processAuthHeader(KerberosAuthenticationFilter.java:95)
at com.organisation.security.kerberos.KerberosAuthenticationFilter.authenticate(KerberosAuthenticationFilter.java:64)
at com.organisation.jaxrs.security.AuthenticationContainerRequestFilter.filter(AuthenticationContainerRequestFilter.java:69)
at org.jboss.resteasy.core.interception.jaxrs.PreMatchContainerRequestContext.filter(PreMatchContainerRequestContext.java:312)
at org.jboss.resteasy.core.SynchronousDispatcher.preprocess(SynchronousDispatcher.java:164)
at org.jboss.resteasy.core.SynchronousDispatcher.invoke(SynchronousDispatcher.java:247)
at org.jboss.resteasy.plugins.server.servlet.ServletContainerDispatcher.service(ServletContainerDispatcher.java:249)
at io.quarkus.resteasy.runtime.ResteasyFilter$ResteasyResponseWrapper.service(ResteasyFilter.java:70)
at io.quarkus.resteasy.runtime.ResteasyFilter$ResteasyResponseWrapper.sendError(ResteasyFilter.java:76)
at io.undertow.servlet.handlers.DefaultServlet.doGet(DefaultServlet.java:172)
at javax.servlet.http.HttpServlet.service(HttpServlet.java:503)
at javax.servlet.http.HttpServlet.service(HttpServlet.java:590)
at io.undertow.servlet.handlers.ServletHandler.handleRequest(ServletHandler.java:74)
at io.undertow.servlet.handlers.FilterHandler$FilterChainImpl.doFilter(FilterHandler.java:129)
at io.quarkus.resteasy.runtime.ResteasyFilter.doFilter(ResteasyFilter.java:31)
at io.undertow.servlet.core.ManagedFilter.doFilter(ManagedFilter.java:61)
at io.undertow.servlet.handlers.FilterHandler$FilterChainImpl.doFilter(FilterHandler.java:131)
at io.undertow.servlet.handlers.FilterHandler.handleRequest(FilterHandler.java:84)
at io.undertow.servlet.handlers.security.ServletSecurityRoleHandler.handleRequest(ServletSecurityRoleHandler.java:63)
at io.undertow.servlet.handlers.ServletChain$1.handleRequest(ServletChain.java:68)
at io.undertow.servlet.handlers.ServletDispatchingHandler.handleRequest(ServletDispatchingHandler.java:36)
at io.undertow.servlet.handlers.RedirectDirHandler.handleRequest(RedirectDirHandler.java:67)
at io.undertow.servlet.handlers.security.SSLInformationAssociationHandler.handleRequest(SSLInformationAssociationHandler.java:133)
at io.undertow.servlet.handlers.security.ServletAuthenticationCallHandler.handleRequest(ServletAuthenticationCallHandler.java:57)
at io.undertow.server.handlers.PredicateHandler.handleRequest(PredicateHandler.java:43)
at io.undertow.security.handlers.AbstractConfidentialityHandler.handleRequest(AbstractConfidentialityHandler.java:46)
at io.undertow.servlet.handlers.security.ServletConfidentialityConstraintHandler.handleRequest(ServletConfidentialityConstraintHandler.java:65)
at io.undertow.security.handlers.AuthenticationMechanismsHandler.handleRequest(AuthenticationMechanismsHandler.java:60)
at io.undertow.servlet.handlers.security.CachedAuthenticatedSessionHandler.handleRequest(CachedAuthenticatedSessionHandler.java:77)
at io.undertow.security.handlers.NotificationReceiverHandler.handleRequest(NotificationReceiverHandler.java:50)
at io.undertow.security.handlers.AbstractSecurityContextAssociationHandler.handleRequest(AbstractSecurityContextAssociationHandler.java:43)
at io.undertow.server.handlers.PredicateHandler.handleRequest(PredicateHandler.java:43)
at io.undertow.server.handlers.PredicateHandler.handleRequest(PredicateHandler.java:43)
at io.undertow.servlet.handlers.ServletInitialHandler.handleFirstRequest(ServletInitialHandler.java:247)
at io.undertow.servlet.handlers.ServletInitialHandler.access$100(ServletInitialHandler.java:56)
at io.undertow.servlet.handlers.ServletInitialHandler$2.call(ServletInitialHandler.java:111)
at io.undertow.servlet.handlers.ServletInitialHandler$2.call(ServletInitialHandler.java:108)
at io.undertow.servlet.core.ServletRequestContextThreadSetupAction$1.call(ServletRequestContextThreadSetupAction.java:48)
at io.undertow.servlet.core.ContextClassLoaderSetupAction$1.call(ContextClassLoaderSetupAction.java:43)
at io.quarkus.undertow.runtime.UndertowDeploymentRecorder$9$1.call(UndertowDeploymentRecorder.java:587)
at io.undertow.servlet.handlers.ServletInitialHandler.dispatchRequest(ServletInitialHandler.java:227)
at io.undertow.servlet.handlers.ServletInitialHandler.handleRequest(ServletInitialHandler.java:152)
at io.quarkus.undertow.runtime.UndertowDeploymentRecorder$1.handleRequest(UndertowDeploymentRecorder.java:119)
at io.undertow.server.Connectors.executeRootHandler(Connectors.java:290)
at io.undertow.server.DefaultExchangeHandler.handle(DefaultExchangeHandler.java:18)
at io.quarkus.undertow.runtime.UndertowDeploymentRecorder$5$1.run(UndertowDeploymentRecorder.java:413)
at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:515)
at java.util.concurrent.FutureTask.run(FutureTask.java:264)
at org.jboss.threads.EnhancedQueueExecutor$Task.run(EnhancedQueueExecutor.java:2415)
at org.jboss.threads.EnhancedQueueExecutor$ThreadBody.run(EnhancedQueueExecutor.java:1452)
at org.jboss.threads.DelegatingRunnable.run(DelegatingRunnable.java:29)
at org.jboss.threads.ThreadLocalResettingRunnable.run(ThreadLocalResettingRunnable.java:29)
at java.lang.Thread.run(Thread.java:834)
at org.jboss.threads.JBossThread.run(JBossThread.java:501)
at com.oracle.svm.core.thread.JavaThreads.threadStartRoutine(JavaThreads.java:519)
at com.oracle.svm.core.posix.thread.PosixJavaThreads.pthreadStartRoutine(PosixJavaThreads.java:192)
Caused by: KrbException: Invalid argument (400) - Cannot find key of appropriate type to decrypt AP-REQ - RC4 with HMAC
at sun.security.krb5.KrbApReq.authenticate(KrbApReq.java:278)
at sun.security.krb5.KrbApReq.<init>(KrbApReq.java:149)
at sun.security.jgss.krb5.InitSecContextToken.<init>(InitSecContextToken.java:139)
at sun.security.jgss.krb5.Krb5Context.acceptSecContext(Krb5Context.java:832)
... 67 more我对Graal相当陌生,也不确定我需要添加什么才能让它工作(或者它是否甚至是当前支持的东西)。
我确实有一些问题要从nad开始--我已经为sun.security.provider.ConfigFile、sun.security.jgss.GSSContextImpl和sun.security.jgss.GSSManagerImpl启用了反射( reflection )来解决它们,不幸的是,我不知道如何处理丢失的键类型。
下面是代码的一个示例
final GSSManager manager = GSSManager.getInstance();
final Oid spnegoOid = new Oid(oid);
final GSSCredential serverCreds = manager.createCredential(null, GSSCredential.DEFAULT_LIFETIME, spnegoOid,
GSSCredential.ACCEPT_ONLY);
final GSSContext context = manager.createContext(serverCreds);
try
{
final byte[] outToken = context.acceptSecContext(inToken, 0, inToken.length);回答 1
Stack Overflow用户
发布于 2021-12-08 07:55:20
linux上运行的Java版本是什么?如果是Java 17或更高版本,这可能是问题所在:
Kerberos
- 在Kerberos中反对3 3DES和RC4 默认情况下,3 3DES和RC4 Kerberos加密类型已被禁用。3 3DES和RC4都是不应该使用的弱加密算法。Kerberos 3 3DES和RC4加密类型在RFC 8429中被正式否决。 默认情况下,des3-hmac-sha1和rc4-hmac加密类型现在是禁用的,但是可以通过在krb5.conf配置文件中将allow_weak_crypto属性设置为true来重新启用,这是您自己的风险。但是,请注意,这也将重新启用其他已禁用的弱加密类型,如des和DE-CBC-MD5。或者,将default_tkt_enctypes、default_tgs_enctypes和permitted_enctypes属性设置为允许的加密类型。 发行:JDK-8139348
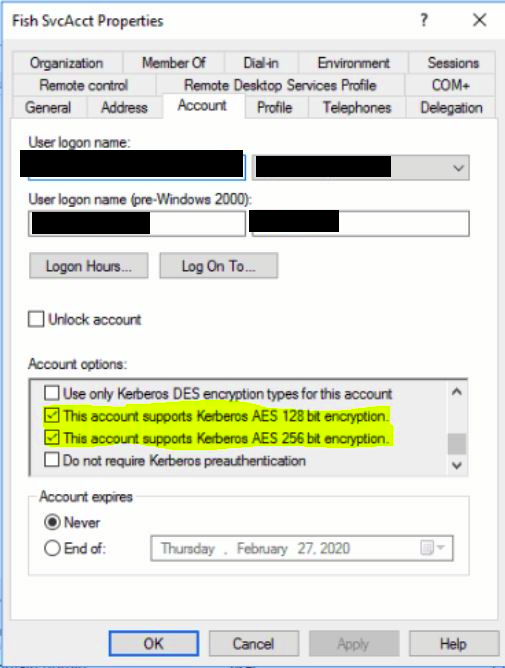
确保检查kerberos-service用户(用于生成keytab文件的用户)的下列选项:
然后,在您的计算机上运行klist purge,并注销/登录当前用户。
可以将以下内容添加到krb5.conf文件中(作为解决办法,不建议这样做):
[libdefaults]
allow_weak_crypto=true此外,还可以使用/crypto ALL使用ktpass命令生成一个新的keytab文件:
ktpass /out "server.keytab" /crypto ALL /princ HTTP/server@REALM /mapuser KERBEROS_SERVICEUSER /pass PASSWORD /ptype KRB5_NT_PRINCIPAL将HTTP/server@REALM、KERBEROS_SERVICEUSER和PASSWORD替换为相应的值。
页面原文内容由Stack Overflow提供。腾讯云小微IT领域专用引擎提供翻译支持
原文链接:
https://stackoverflow.com/questions/67642724
复制相关文章
相似问题

