使用S3桶服务资产的Serverless
我使用Bref (https://bref.sh/)。我尝试使用serverless.yml AWS S3配置文件,以便存储诸如img、css、js等资产。当我使用“无服务器部署”命令进行部署时,我有以下错误:
发生了一个错误: AssetsBucketPolicy - API: s3:PutBucketPolicy访问被拒绝。
在我的AWS帐户中,我有"AdministratorAccess“权限(-jlAhLRgEcU0P0Ivi4OO844pgrzJOU&index=2&t=0s)
战略AdministratorAccess
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": "*",
"Resource": "*"
}
]
}我的serverless.yml文件是:
service: bref-demo-symfony
provider:
name: aws
region: us-east-1
runtime: provided
environment:
# Symfony environment variables
APP_ENV: prod
plugins:
- ./vendor/bref/bref
functions:
website:
handler: public/index.php
timeout: 28 # in seconds (API Gateway has a timeout of 29 seconds)
layers:
- ${bref:layer.php-73-fpm}
events:
- http: 'ANY /'
- http: 'ANY /{proxy+}'
console:
handler: bin/console
timeout: 120 # in seconds
layers:
- ${bref:layer.php-73} # PHP
- ${bref:layer.console} # The "console" layer
resources:
Resources:
# The S3 bucket that stores the assets
Assets:
Type: AWS::S3::Bucket
Properties:
BucketName: my-unique-serverless-assets-bucket
# The policy that makes the bucket publicly readable
AssetsBucketPolicy:
Type: AWS::S3::BucketPolicy
Properties:
Bucket: !Ref Assets # References the bucket we defined above
PolicyDocument:
Statement:
- Effect: Allow
Principal: '*' # everyone
Action: 's3:GetObject' # to read
Resource: 'arn:aws:s3:::my-unique-serverless-assets-bucket/*' # things in the bucket在AWS S3上,我尝试在桶上添加一个策略
{
"Id": "Policy1573043469280",
"Version": "2012-10-17",
"Statement": [
{
"Sid": "Stmt1573043465451",
"Action": "s3:*",
"Effect": "Allow",
"Resource": "arn:aws:s3:::bref-demo-symfony-dev-serverless-assets/assets",
"Principal": "*"
}
]
}我有一条类似于“拒绝访问”的消息,“您不能授予公共访问权限,因为该帐户打开了块公共访问设置。要确定打开了哪些设置,请检查您的块公共访问设置。”为什么?
我不知道怎么配置它?这个权限(AdministratorAccess)还不够吗?
谢谢!
回答 3
Stack Overflow用户
发布于 2019-11-06 01:31:36
从文档中,您可以看到:
若要解决“拒绝访问”错误,请检查以下内容: 您的IAM身份同时具有
s3:GetBucketPolicy和s3:PutBucketPolicy的权限。 https://aws.amazon.com/premiumsupport/knowledge-center/s3-access-denied-bucket-policy/
请检查为Lambda函数配置的角色是否具有此权限。
您可以在“执行角色”部分看到这一点:
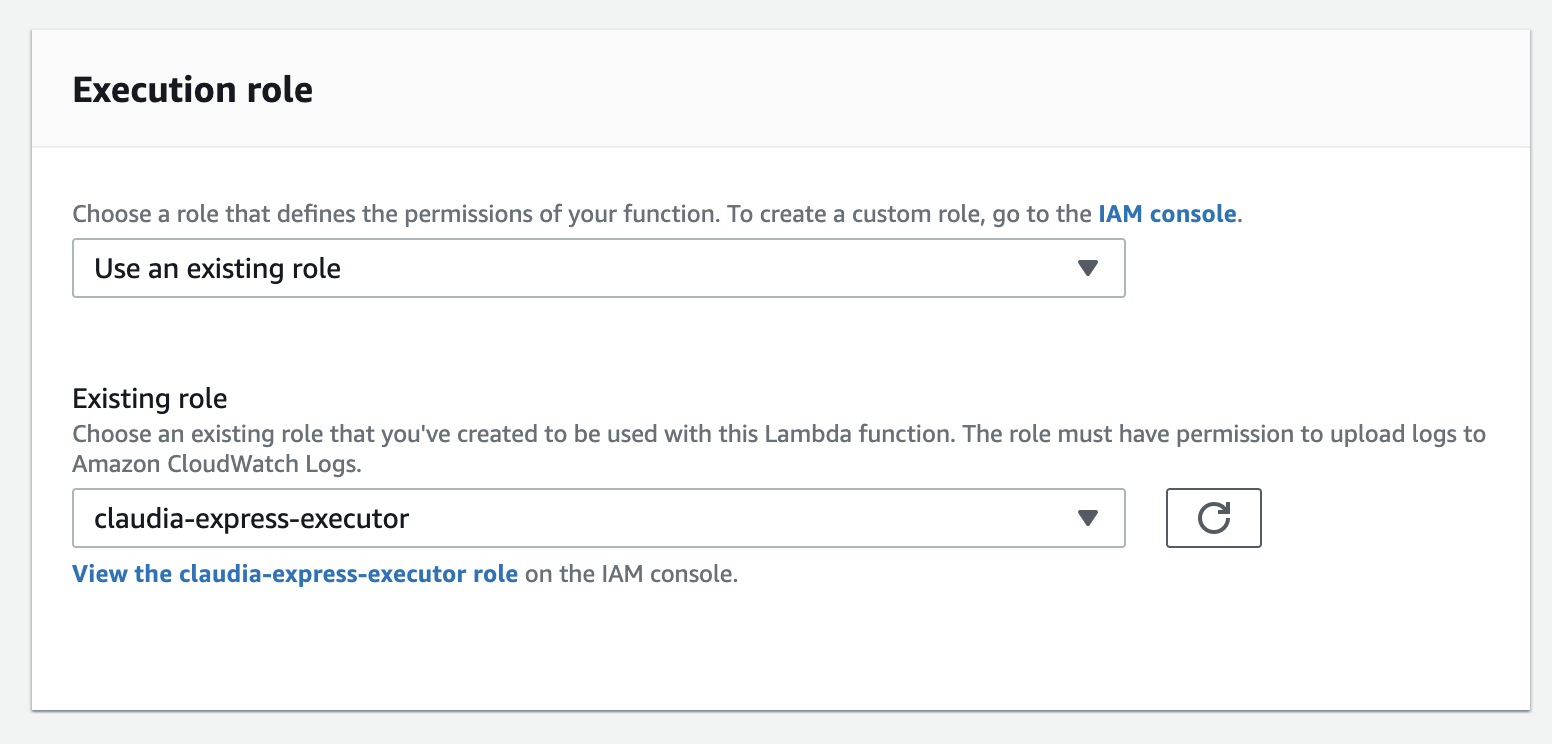
在这里你可以看到我的Lambda函数有一个角色"claudia-express-executor“。
您还可以单击它,并详细检查角色权限是什么。
Stack Overflow用户
发布于 2019-11-06 02:15:06
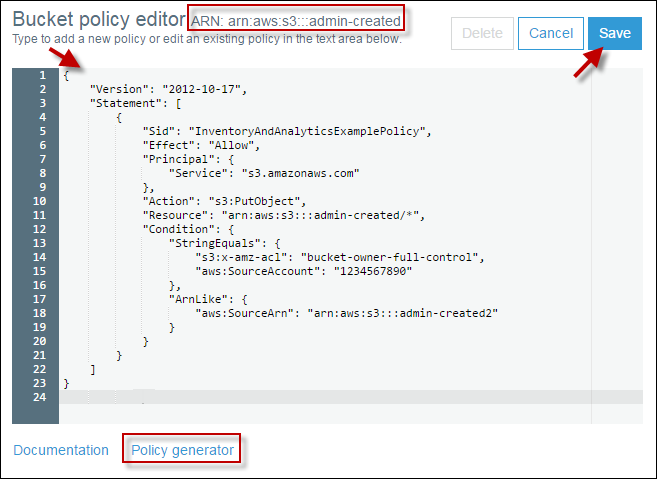
- 检查水桶政策
- 如果涉及桶策略,则添加您为无服务器服务器创建的用户。
- 查看下面的图像以获得样例桶策略https://docs.aws.amazon.com/AmazonS3/latest/user-guide/add-bucket-policy.html
Stack Overflow用户
发布于 2019-11-06 05:54:37
例如,如果需要get和put对象,请尝试添加iamRoleStatements,在iamRoleStatements上添加以下代码,例如:
provider:
name: aws
runtime: nodejs10.x
region: us-west-2
profile: ${self:custom.profiles.${self:custom.myStage}}
iamRoleStatements:
- Effect: "Allow"
Action:
- "s3:PutObject"
- "s3:GetObject"
Resource:
- "*"这是另一个例子:
provider:
name: aws
iamRoleStatements:
- Effect: 'Allow'
Action:
- 's3:ListBucket'
Resource:
Fn::Join:
- ''
- - 'arn:aws:s3:::'
- Ref: ServerlessDeploymentBucket
- Effect: 'Allow'
Action:
- 's3:PutObject'
Resource:
Fn::Join:
- ''
- - 'arn:aws:s3:::'
- Ref: ServerlessDeploymentBucket
- '/*'如果需要更多信息,请阅读无服务器文档:无服务器IAM角色
https://stackoverflow.com/questions/58716260
复制相似问题

