禁止使用荚:用户"system:serviceaccount:kubernetes-dashboard:admin-user“不能将API组中的资源" pods”列在名称空间"default“中。
我试图通过遵循这篇文章在Ubuntu18.04上设置Kubernetes。
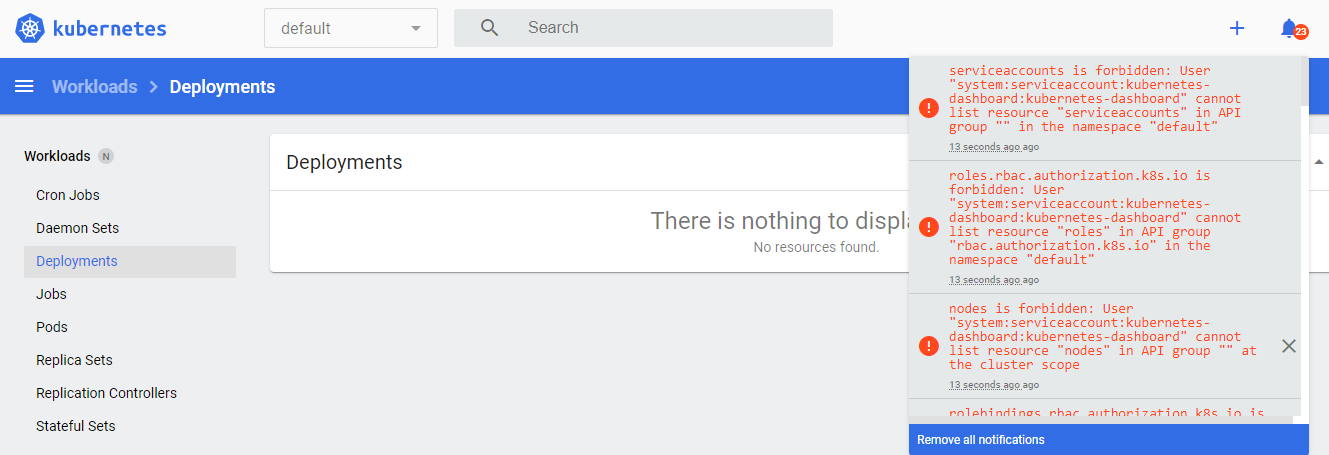
一切都很好,但是当我试图访问本地Kubernetes仪表板时,它会显示为空的,没有任何东西可以像豆荚、服务和部署那样可见。
然而,当我运行$> kubectl get pods,svc,deployments时,它显示了下面的output.If命令行显示了为什么我看到空的Kubernetes仪表板的所有细节?
我已经运行了以下命令
$> kubectl apply -f https://raw.githubusercontent.com/kubernetes/dashboard/v2.0.0-beta8/aio/deploy/recommended.yaml
$> kubectl proxy我在这里缺少任何配置吗?有什么解决这个问题的建议吗?
$> kubectl get pods --all-namespaces
NAMESPACE NAME READY STATUS RESTARTS AGE
kubernetes-dashboard dashboard-metrics-scraper-76585494d8-4rrdp 1/1 Running 3 46h
kubernetes-dashboard kubernetes-dashboard-5996555fd8-sxgxf 1/1 Running 16 46h查看通知部分后,发现以下错误
- 事件被禁止:用户"system:serviceaccount:kubernetes-dashboard:admin-user“不能在API组"”名称空间“默认”中列出资源" events“。
- 禁止使用荚:用户"system:serviceaccount:kubernetes-dashboard:admin-user“不能将API组中的资源" pods”列在名称空间"default“中。
更新1:
其工作于应用RBAC kubectl后应用-f filename.yml。
apiVersion: v1
kind: ServiceAccount
metadata:
name: admin-user
namespace: kube-system
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRoleBinding
metadata:
name: admin-user
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-admin
subjects:
- kind: ServiceAccount
name: admin-user
namespace: kube-system回答 2
Stack Overflow用户
发布于 2020-01-06 00:08:34
您可能需要将仪表板服务帐户绑定到集群管理角色:
kubectl create clusterrolebinding dashboard-admin-sa --clusterrole=cluster-admin --serviceaccount=default:dashboard-admin-sa
否则,仪表板服务帐户无法访问填充仪表板的数据。
Stack Overflow用户
发布于 2021-01-04 19:39:53
我是根据使用v2.1.0和K8s v1.20的经验来回答这个问题的。安装kubernetes-仪表板时,它创建了一个服务帐户和两个名为“kubernetes-仪表板”的角色,并将角色与仪表板命名空间绑定,另一个角色绑定到集群范围的角色(但不是集群-admin)。因此,不幸的是,权限不足以管理整个集群,如下所示:
安装日志:
$ kubectl apply -f https://raw.githubusercontent.com/kubernetes/dashboard/v2.1.0/aio/deploy/recommended.yaml
namespace/kubernetes-dashboard created
serviceaccount/kubernetes-dashboard created
service/kubernetes-dashboard created
secret/kubernetes-dashboard-certs created
secret/kubernetes-dashboard-csrf created
secret/kubernetes-dashboard-key-holder created
configmap/kubernetes-dashboard-settings created
role.rbac.authorization.k8s.io/kubernetes-dashboard created
clusterrole.rbac.authorization.k8s.io/kubernetes-dashboard created
rolebinding.rbac.authorization.k8s.io/kubernetes-dashboard created
clusterrolebinding.rbac.authorization.k8s.io/kubernetes-dashboard created
deployment.apps/kubernetes-dashboard created
service/dashboard-metrics-scraper created
deployment.apps/dashboard-metrics-scraper created查看您看到的权限:
$ kubectl describe clusterrole kubernetes-dashboard
Name: kubernetes-dashboard
Labels: k8s-app=kubernetes-dashboard
Annotations: <none>
PolicyRule:
Resources Non-Resource URLs Resource Names Verbs
--------- ----------------- -------------- -----
nodes.metrics.k8s.io [] [] [get list watch]
pods.metrics.k8s.io [] [] [get list watch]
$ kubectl describe role kubernetes-dashboard -n kubernetes-dashboard
Name: kubernetes-dashboard
Labels: k8s-app=kubernetes-dashboard
Annotations: <none>
PolicyRule:
Resources Non-Resource URLs Resource Names Verbs
--------- ----------------- -------------- -----
secrets [] [kubernetes-dashboard-certs] [get update delete]
secrets [] [kubernetes-dashboard-csrf] [get update delete]
secrets [] [kubernetes-dashboard-key-holder] [get update delete]
configmaps [] [kubernetes-dashboard-settings] [get update]
services/proxy [] [dashboard-metrics-scraper] [get]
services/proxy [] [heapster] [get]
services/proxy [] [http:dashboard-metrics-scraper] [get]
services/proxy [] [http:heapster:] [get]
services/proxy [] [https:heapster:] [get]
services [] [dashboard-metrics-scraper] [proxy]
services [] [heapster] [proxy]与其使kubernetes-仪表板服务帐户成为群集管理帐户(因为该帐户用于数据收集),更好的方法是创建一个只有令牌的新服务帐户,并且可以轻松地撤销帐户,而不是更改预先创建的帐户的权限。
要创建一个名为"dashboard-admin“的新服务帐户,并以声明方式应用:
$ nano dashboard-svcacct.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
name: dashboard-admin
namespace: kubernetes-dashboard
$ kubectl apply -f dashboard-svcacct.yaml
serviceaccount/dashboard-admin created若要将新服务帐户绑定到群集管理角色,请执行以下操作:
$ nano dashboard-binding.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: dashboard-admin
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-admin
subjects:
- kind: ServiceAccount
name: dashboard-admin
namespace: kubernetes-dashboard
$ kubectl apply -f dashboard-binding.yaml
clusterrolebinding.rbac.authorization.k8s.io/dashboard-admin created若要从此服务帐户提取令牌,可用于登录:
$ kubectl -n kubernetes-dashboard describe secret $(kubectl -n kubernetes-dashboard get secret | grep dashboard-admin | awk '{print $1}')
Name: dashboard-admin-token-4fxtt
Namespace: kubernetes-dashboard
Labels: <none>
Annotations: kubernetes.io/service-account.name: dashboard-admin
kubernetes.io/service-account.uid: 9cd5bb80-7901-413b-9eac-7b72c353d4b9
Type: kubernetes.io/service-account-token
Data
====
ca.crt: 1066 bytes
namespace: 20 bytes
token: eyJhbGciOiJSUzI1NiIsImtpZCI6Ikp3ZERpQTFPOV<REDACTED>以"eyJ“开头的整个令牌现在可以用于登录:
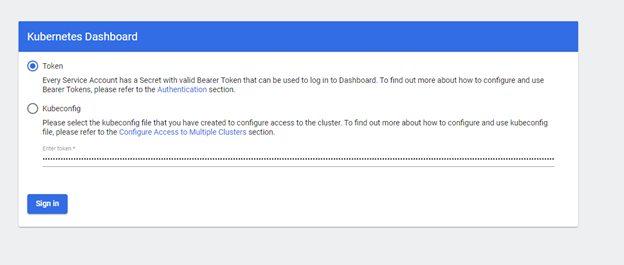
但是,令牌登录的剪切和粘贴可能会在后面造成痛苦,特别是在默认超时的情况下。我更喜欢配置文件。对于此选项,将需要集群CA哈希。此配置文件的集群部分与~/..kube/ config下的配置文件相同。这个配置文件不需要加载到kubernetes主服务器,只需要在工作站上使用正在访问仪表板的浏览器。我将其命名为dashboard-config,并使用VS代码创建它(任何编辑器,只需确保您打开文本以确保散列值中没有空格)。如果复制配置文件,则不需要将任何admin CA和私钥散列保存在users:。
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: <CLUSTER CA HASH HERE>
server: https://<IP ADDR OF CLUSTER>:6443
name: kubernetes #name of cluster
contexts:
- context:
cluster: kubernetes
user: dashboard-admin
name: dashboard-admin@kubernetes
current-context: dashboard-admin@kubernetes
kind: Config
preferences: {}
users:
- name: kubernetes-dashboard
user:
token: <TOKEN HASH from above command e.g. eyJ>现在起作用了。
https://stackoverflow.com/questions/59605085
复制相似问题

