会话:调用TargetNotConnected操作时发生错误( StartSession操作:<instance_id>未连接)
问题:
当我尝试使用AWS系统会话管理器CLI命令在本地连接到正在运行的EC2实例时:aws ssm start-session --target i-123456
我知道错误:
An error occurred (TargetNotConnected) when calling the StartSession operation: i-123456 is not connected.背景:
- 托管在自定义VPC中的私有子网上的Linux 2实例
- VPC 端点用于将系统管理器连接到托管实例,而不需要NAT、GW或IGW。
- 端点服务名称:
com.amazonaws.us-west-2.s3
com.amazonaws.us-west-2.ec2
com.amazonaws.us-west-2.ec2messages
com.amazonaws.us-west-2.ssm
com.amazonaws.us-west-2.ssmmessages- AWS CLI == 2.0.40
- Python == 3.7.4
- 自定义Terraform模块用于在一个专用子网中启动气流实例(请参阅下面的模块"airflow_aws_resources“)
- 与此问题相关的唯一.tf文件是模块"airflow_aws_resources“中的airflow.tf。此文件包含通过SSM连接的EC2实例的安全组和实例配置文件配置。
用Terraform复制:
module "airflow_aws_resources" {
source = "github.com/marshall7m/tf_modules/airflow-aws-resources"
resource_prefix = "test"
vpc_id = module.vpc.vpc_id
env = "testing"
private_bucket = "test-bucket"
private_subnets_ids = module.vpc.private_subnets
private_subnets_cidr_blocks = module.vpc.private_subnets_cidr_blocks
create_airflow_instance = true
create_airflow_instance_sg = true
create_airflow_db = false
create_airflow_db_sg = false
airflow_instance_ssm_access = true
airflow_instance_ssm_region = "us-west-2"
airflow_instance_ami = "ami-0841edc20334f9287"
airflow_instance_type = "t2.micro"
}
resource "aws_security_group" "vpc_endpoints" {
name = "test-vpc-endpoint-sg"
description = "Default security group for vpc endpoints"
vpc_id = module.vpc.vpc_id
ingress {
from_port = 80
to_port = 80
protocol = "tcp"
cidr_blocks = ["10.0.0.32/28", "10.0.0.64/28"]
}
ingress {
from_port = 443
to_port = 443
protocol = "tcp"
#private subnet cidr blocks
cidr_blocks = ["10.0.0.32/28", "10.0.0.64/28"]
}
egress {
from_port = 443
to_port = 443
protocol = "tcp"
cidr_blocks = ["10.0.0.32/28", "10.0.0.64/28"]
}
egress {
from_port = 80
to_port = 80
protocol = "tcp"
cidr_blocks = ["10.0.0.32/28", "10.0.0.64/28"]
}
}
module "vpc" {
source = "terraform-aws-modules/vpc/aws"
version = "2.44.0"
name = "test-vpc"
cidr = "10.0.0.0/24"
azs = ["us-west-2a", "us-west-2b"]
private_subnets = ["10.0.0.32/28", "10.0.0.64/28"]
private_dedicated_network_acl = true
private_subnet_suffix = "private"
public_subnets = ["10.0.0.96/28", "10.0.0.128/28"]
public_dedicated_network_acl = true
public_subnet_suffix = "public"
enable_s3_endpoint = true
enable_ec2messages_endpoint = true
ec2messages_endpoint_security_group_ids = [aws_security_group.vpc_endpoints.id]
enable_ec2_endpoint = true
ec2_endpoint_security_group_ids = [aws_security_group.vpc_endpoints.id]
enable_ssm_endpoint = true
ssm_endpoint_security_group_ids = [aws_security_group.vpc_endpoints.id]
enable_ssmmessages_endpoint = true
ssmmessages_endpoint_security_group_ids = [aws_security_group.vpc_endpoints.id]
enable_nat_gateway = false
single_nat_gateway = false
enable_vpn_gateway = false
create_database_subnet_route_table = false
create_database_internet_gateway_route = false
create_database_subnet_group = false
manage_default_network_acl = false
enable_dns_hostnames = true
enable_dns_support = true
private_inbound_acl_rules = [
{
"description": "Allows inbound https traffic for aws s3 package requests"
"cidr_block": "0.0.0.0/0",
"from_port": 443,
"to_port": 443,
"protocol": "tcp",
"rule_action": "allow",
"rule_number": 101
},
{
"description": "Allows inbound http traffic for aws s3 package requests"
"cidr_block": "0.0.0.0/0",
"from_port": 80,
"to_port": 80,
"protocol": "tcp",
"rule_action": "allow",
"rule_number": 102
}
]
private_outbound_acl_rules = [
{
"description": "Allows outbound https traffic for aws s3 package requests"
"cidr_block": "0.0.0.0/0",
"from_port": 443,
"to_port": 443,
"protocol": "tcp",
"rule_action": "allow",
"rule_number": 101
},
{
"description": "Allows outbound http traffic for aws s3 package requests"
"cidr_block": "0.0.0.0/0",
"from_port": 80,
"to_port": 80,
"protocol": "tcp",
"rule_action": "allow",
"rule_number": 102
}
]
vpc_endpoint_tags = {
type = "vpc-endpoint"
}
}尝试:
#1
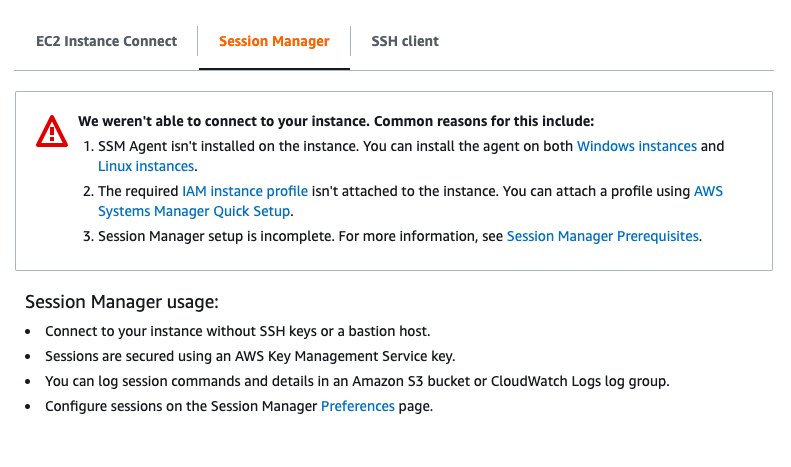
我在EC2控制台SSM (AWS Ec2 Console >> instance-id >> Connect >> Session Manager)中尝试了解决问题的技巧:
- SSM代理已经预装在AWS Linux实例类型上。虽然我通过SSH访问实例并运行
sudo status amazon-ssm-agent(返回:amazon-ssm-agent start/running, process 1234)使检查加倍 - 上面显示的EC2实例配置文件包括所需的
AmazonSSMManagedInstanceCore策略。 - 我完成了会话管理器的先决条件。
#2
使用以下命令将AmazonSSMFullAccess附加到用户:aws ssm start-session --target i-123456
通过SSM连接实例时相同的错误:
An error occurred (TargetNotConnected) when calling the StartSession operation: i-123456 is not connected.#3
将HTTPS入站/出站流量从VPC端点的经过合并的私有子网添加到EC2实例安全组(请参阅airflow.tf)
同样的错误:
An error occurred (TargetNotConnected) when calling the StartSession operation: i-123456 is not connected.#4
在“系统管理器”控制台中,我使用了“快速设置”选项,并使用airflow.tf中指定的实例配置文件和默认角色配置了“系统管理器”角色。ec2实例成功地在快速设置页面中注册了“托管实例”。
同样的错误:
An error occurred (TargetNotConnected) when calling the StartSession operation: i-123456 is not connected.#5
考虑到这是一个测试VPC和EC2实例,我尝试允许来自所有IPv4源的所有类型的通信量(0.0.0.0/0)用于以下资源:
- 私有子网NACL
- EC2实例安全组
- 与以下接口/网关端点相关联的安全组:
com.amazonaws.us-west-2.s3
com.amazonaws.us-west-2.ec2
com.amazonaws.us-west-2.ec2messages
com.amazonaws.us-west-2.ssm
com.amazonaws.us-west-2.ssmmessages通过SSM连接实例时相同的错误:
An error occurred (TargetNotConnected) when calling the StartSession operation: i-123456 is not connected.回答 10
Stack Overflow用户
发布于 2021-03-26 13:59:43
我会请参阅这里,以确保您的一切设置正确。我首先要添加配置文件参数。如果这仍然不起作用,当我的概要文件默认区域不是我希望开始活动会话的区域时,我遇到了类似的问题。因此,我也需要使用区域参数。示例. .ssh/config如下:
host ssh i-abc123
ProxyCommand sh -c "aws --region desired_region --profile my_profile ssm start-session --target %h --document-name AWS-StartSSHSession --parameters 'portNumber=%p'"我还鼓励使用AWS v2。配置. .ssh/config后,只需在CLI中执行以下操作:
ssh i-abc123Stack Overflow用户
发布于 2020-10-03 04:55:41
所以你可能需要使用个人资料。我使用OSX上的AWS CLI通过终端连接到VPC中的linux主机。这是一个只能通过SSO访问的帐户。我能够创建一个概要文件,并且在通过CLI对SSO进行身份验证之后,我可以建立这样的连接。
做一次
aws sso login --profile my_customer 然后,使用一个简单的命令(在我的osx终端上)验证sso登录是否成功。
aws s3 ls --profile my_customer custbucket-s3-sftp/rds/现在建立会话管理器连接
aws ssm start-session --profile my_customer --target i-0012345abcdef890我知道您正在使用python,但这可能会有所帮助。
Stack Overflow用户
发布于 2021-05-06 07:52:00
在某些情况下,您必须验证以下内容:
- AWS帐户/概况
- AWS区
在一个案例中,我发现它试图连接到aws配置文件。
后来,在其他情况下,我连接到一个不同的区域。
https://stackoverflow.com/questions/64001338
复制相似问题

