如何监控网络流量和浏览器活动?
首先,让我告诉大家我想做什么,我在哪里挣扎。
1.我想在web浏览器中跟踪用户的移动。
- 在任何浏览器中,我都想保存关于用户登录的网站、包数据(下载/上传)、用户正在使用的浏览器的信息。
- 我想记录信息,例如我在第2项中提到的协议,本地端口,本地地址和远程端口,远程端口名,远程地址,发送的数据包和接收的数据包。
我分享了我想做的和不能做的。
我尝试过的方法;我尝试在google,edge,opera浏览器中执行api钩子操作。
我已将蹦床函数方法应用于winhttp.dll函数,但无法获得任何数据。
static DWORD(WINAPI* MS_WinHttpWebSocketReceive)(HINTERNET hWebSocket,
PVOID pvBuffer,
DWORD dwBufferLength,
DWORD* pdwBytesRead,
WINHTTP_WEB_SOCKET_BUFFER_TYPE* peBufferType
) = WinHttpWebSocketReceive;
static DWORD WINAPI MY_WinHttpWebSocketReceive(HINTERNET hWebSocket,
PVOID pvBuffer,
DWORD dwBufferLength,
DWORD* pdwBytesRead,
WINHTTP_WEB_SOCKET_BUFFER_TYPE* peBufferType)
{
OutputDebugString(L"=====MY_WinHttpWebSocketReceive Start======");
OutputDebugString(L"Succeed");
OutputDebugString(L"=====MY_WinHttpWebSocketReceive End======");
return MS_WinHttpWebSocketReceive(hWebSocket, pvBuffer, dwBufferLength, pdwBytesRead, peBufferType);
}我尝试了蹦床函数法对winhttp.dll的许多功能,但失败了。
有人知道他们在我共享的应用程序中使用哪种方法吗?
我怎么才能做我想做的事?
我需要连接哪些dll和函数来获取我想要的信息?
我想保存诸如协议、本地端口、本地地址和远程端口、远程端口名、远程地址、发送的数据包和接收的数据包等信息。
给我看看兔子洞。
回答 1
Stack Overflow用户
发布于 2020-11-19 07:31:20
看起来,您正在寻找一个类似于网络监视器3工具的实现。
您可以开始从Windows套接字2学习。如果您想要快速完成项目,那么您可以专注于以下API。
其中,recvfrom接受的缓冲区是我们所需要的。
recvfrom函数读取连接和未连接套接字上的传入数据,并捕获发送数据的地址。此函数通常用于无连接套接字。 对于面向消息的套接字,从第一个排队消息中提取数据,直到指定缓冲区的大小为止。如果数据报或消息大于指定的缓冲区,则缓冲区将填充数据报的第一部分,recvfrom将生成错误WSAEMSGSIZE。对于不可靠的协议(例如,UDP),会丢失多余的数据。对于UDP,如果接收到的数据包不包含数据(空),则recvfrom函数的返回值为零。 。。
当然,我们需要一个适当的例子来帮助我们向前迈进。
一些代码:
typedef struct ip_hdr
{
unsigned char ip_header_len : 4; // 4-bit header length (in 32-bit words) normally=5 (Means 20 Bytes may be 24 also)
unsigned char ip_version : 4; // 4-bit IPv4 version
unsigned char ip_tos; // IP type of service
unsigned short ip_total_length; // Total length
unsigned short ip_id; // Unique identifier
unsigned char ip_frag_offset : 5; // Fragment offset field
unsigned char ip_more_fragment : 1;
unsigned char ip_dont_fragment : 1;
unsigned char ip_reserved_zero : 1;
unsigned char ip_frag_offset1; //fragment offset
unsigned char ip_ttl; // Time to live
unsigned char ip_protocol; // Protocol(TCP,UDP etc)
unsigned short ip_checksum; // IP checksum
unsigned int ip_srcaddr; // Source address
unsigned int ip_destaddr; // Source address
} IPV4_HDR;
typedef struct udp_hdr
{
unsigned short source_port; // Source port no.
unsigned short dest_port; // Dest. port no.
unsigned short udp_length; // Udp packet length
unsigned short udp_checksum; // Udp checksum (optional)
} UDP_HDR;
// TCP header
typedef struct tcp_header
{
unsigned short source_port; // source port
unsigned short dest_port; // destination port
unsigned int sequence; // sequence number - 32 bits
unsigned int acknowledge; // acknowledgement number - 32 bits
unsigned char ns : 1; //Nonce Sum Flag Added in RFC 3540.
unsigned char reserved_part1 : 3; //according to rfc
unsigned char data_offset : 4; /*The number of 32-bit words in the TCP header.
This indicates where the data begins.
The length of the TCP header is always a multiple
of 32 bits.*/
unsigned char fin : 1; //Finish Flag
unsigned char syn : 1; //Synchronise Flag
unsigned char rst : 1; //Reset Flag
unsigned char psh : 1; //Push Flag
unsigned char ack : 1; //Acknowledgement Flag
unsigned char urg : 1; //Urgent Flag
unsigned char ecn : 1; //ECN-Echo Flag
unsigned char cwr : 1; //Congestion Window Reduced Flag
////////////////////////////////
unsigned short window; // window
unsigned short checksum; // checksum
unsigned short urgent_pointer; // urgent pointer
} TCP_HDR;
...
int main()
{
SOCKET sniffer;
struct in_addr addr;
int in;
char hostname[100];
struct hostent* local;
WSADATA wsa;
logfile = fopen("log.txt", "w");
if (logfile == NULL)
{
printf("Unable to create file.");
}
//Initialise Winsock
printf("\nInitialising Winsock...");
if (WSAStartup(MAKEWORD(2, 2), &wsa) != 0)
{
printf("WSAStartup() failed.\n");
return 1;
}
printf("Initialised");
//Create a RAW Socket
printf("\nCreating RAW Socket...");
sniffer = socket(AF_INET, SOCK_RAW, IPPROTO_IP);
if (sniffer == INVALID_SOCKET)
{
printf("Failed to create raw socket.\n");
return 1;
}
printf("Created.");
//Retrive the local hostname
if (gethostname(hostname, sizeof(hostname)) == SOCKET_ERROR)
{
printf("Error : %d", WSAGetLastError());
return 1;
}
printf("\nHost name : %s \n", hostname);
//Retrive the available IPs of the local host
local = gethostbyname(hostname);
printf("\nAvailable Network Interfaces : \n");
if (local == NULL)
{
printf("Error : %d.\n", WSAGetLastError());
return 1;
}
for (i = 0; local->h_addr_list[i] != 0; ++i)
{
memcpy(&addr, local->h_addr_list[i], sizeof(struct in_addr));
printf("Interface Number : %d Address : %s\n", i, inet_ntoa(addr));
}
printf("Enter the interface number you would like to sniff : ");
scanf("%d", &in);
memset(&dest, 0, sizeof(dest));
memcpy(&dest.sin_addr.s_addr, local->h_addr_list[in], sizeof(dest.sin_addr.s_addr));
dest.sin_family = AF_INET;
dest.sin_port = 0;
printf("\nBinding socket to local system and port 0 ...");
if (bind(sniffer, (struct sockaddr*) & dest, sizeof(dest)) == SOCKET_ERROR)
{
printf("bind(%s) failed.\n", inet_ntoa(addr));
return 1;
}
printf("Binding successful");
//Enable this socket with the power to sniff : SIO_RCVALL is the key Receive ALL ;)
j = 1;
printf("\nSetting socket to sniff...");
if (WSAIoctl(sniffer, SIO_RCVALL, &j, sizeof(j), 0, 0, (LPDWORD)&in, 0, 0) == SOCKET_ERROR)
{
printf("WSAIoctl() failed.\n");
return 1;
}
printf("Socket set.");
//Begin
printf("\nStarted Sniffing\n");
printf("Packet Capture Statistics...\n");
StartSniffing(sniffer);
//End
closesocket(sniffer);
WSACleanup();
return 0;
}完整代码:winsock样本 (开箱即用)不要忘记以admin.的身份运行
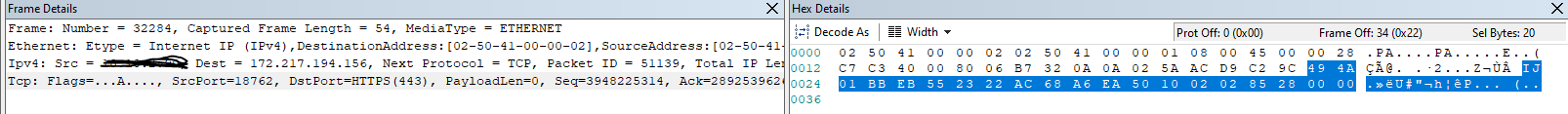
您还可以使用Network 3.4工具来理解缓冲区结构。
https://stackoverflow.com/questions/64889982
复制相似问题

