为什么我的SIMCard返回6985到外部身份验证APDU命令?
为什么我的SIMCard返回6985到外部身份验证APDU命令?
提问于 2021-07-10 11:12:57
我有一个基于Javacard的SIM卡,其规范如下:
D:\>gp -i
# GlobalPlatformPro 325fe84
# Running on Windows 8.1 6.3 amd64, Java 1.8.0_20 by Oracle Corporation
Unlimited crypto policy is NOT installed!
IIN: <Censored by OP>
CIN: <Censored by OP>
Card Data:
Tag 6: 1.2.840.114283.1
-> Global Platform card
Tag 60: 1.2.840.114283.2.2.2
-> GP Version: 2.2
Tag 63: 1.2.840.114283.3
Tag 64: 1.2.840.114283.4.0
-> GP SCP80 i=00
Tag 64: 1.2.840.114283.4.2.21
-> GP SCP02 i=15
Tag 65: 1.2.840.114283.5.4
Tag 66: 1.3.6.1.4.1.42.2.110.1.2
-> JavaCard v2
Card Capabilities:
[WARN] GPKeyInfo - Access and Usage not parsed: 01180100
[WARN] GPKeyInfo - Access and Usage not parsed: 01140100
[WARN] GPKeyInfo - Access and Usage not parsed: 01480100
[WARN] GPKeyInfo - Access and Usage not parsed: 01180100
[WARN] GPKeyInfo - Access and Usage not parsed: 01140100
[WARN] GPKeyInfo - Access and Usage not parsed: 01480100
Version: 32 (0x20) ID: 1 (0x01) type: DES3 length: 16
Version: 32 (0x20) ID: 2 (0x02) type: DES3 length: 16
Version: 32 (0x20) ID: 3 (0x03) type: DES3 length: 16
Version: 33 (0x21) ID: 1 (0x01) type: DES3 length: 16
Version: 33 (0x21) ID: 2 (0x02) type: DES3 length: 16
Version: 33 (0x21) ID: 3 (0x03) type: DES3 length: 16
Version: 34 (0x22) ID: 1 (0x01) type: DES3 length: 16
Version: 34 (0x22) ID: 2 (0x02) type: DES3 length: 16
Version: 34 (0x22) ID: 3 (0x03) type: DES3 length: 16
Version: 35 (0x23) ID: 1 (0x01) type: DES3 length: 16
Version: 35 (0x23) ID: 2 (0x02) type: DES3 length: 16
Version: 35 (0x23) ID: 3 (0x03) type: DES3 length: 16
Version: 1 (0x01) ID: 1 (0x01) type: DES3 length: 16
Version: 1 (0x01) ID: 2 (0x02) type: DES3 length: 16
Version: 1 (0x01) ID: 3 (0x03) type: DES3 length: 16
Version: 2 (0x02) ID: 1 (0x01) type: DES3 length: 16
Version: 2 (0x02) ID: 2 (0x02) type: DES3 length: 16
Version: 2 (0x02) ID: 3 (0x03) type: DES3 length: 16
Version: 3 (0x03) ID: 1 (0x01) type: DES3 length: 16
Version: 3 (0x03) ID: 2 (0x02) type: DES3 length: 16
Version: 3 (0x03) ID: 3 (0x03) type: DES3 length: 16
Version: 4 (0x04) ID: 1 (0x01) type: DES3 length: 16
Version: 4 (0x04) ID: 2 (0x02) type: DES3 length: 16
Version: 4 (0x04) ID: 3 (0x03) type: DES3 length: 16
Version: 5 (0x05) ID: 1 (0x01) type: DES3 length: 16
Version: 5 (0x05) ID: 2 (0x02) type: DES3 length: 16
Version: 5 (0x05) ID: 3 (0x03) type: DES3 length: 16
Version: 6 (0x06) ID: 1 (0x01) type: DES3 length: 16
Version: 6 (0x06) ID: 2 (0x02) type: DES3 length: 16
Version: 6 (0x06) ID: 3 (0x03) type: DES3 length: 16
Version: 7 (0x07) ID: 1 (0x01) type: DES3 length: 16
Version: 7 (0x07) ID: 2 (0x02) type: DES3 length: 16
Version: 7 (0x07) ID: 3 (0x03) type: DES3 length: 16
Version: 8 (0x08) ID: 1 (0x01) type: DES3 length: 16
Version: 8 (0x08) ID: 2 (0x02) type: DES3 length: 16
Version: 8 (0x08) ID: 3 (0x03) type: DES3 length: 16
Warning: no keys given, defaulting to 404142434445464748494A4B4C4D4E4F当我想使用它进行相互认证时,我会收到69 85 (使用条件不满足)错误状态词:
D:\>python mutual_auth.py
Connected to Card with ATR = 3B9F95803FC6A08031E073FE211B670110B26094101401
---> 00 A4 04 00 08 A0 00 00 00 03 00 00 00
<--- 6F 10 84 08 A0 00 00 00 03 00 00 00 A5 04 9F 65 01 FF 90 00
---> 80 50 00 00 08 37 CD BA 7B B4 57 B5 1B
<--- 00 00 C6 D8 6A 1C B2 02 14 13 20 02 00 00 71 90 98 C2 77 8A 07 3D 4A 4B F1 4D D4 FB 90 00
:: Calculated "Session Keys" based on host and card challenges:
Session ENC: 43cc9d7949a13e83d22626400645c4c143cc9d7949a13e83
Session MAC: 4abaaa3864d8fbf2ae0ac430c550ef564abaaa3864d8fbf2
Session DEK: e1fbe0ccb299f3dcf756308f94fa4fb5e1fbe0ccb299f3dc
:: Card cryptogram verified successfully.
---> 84 82 00 00 10 22 66 0D BB EF 34 74 D3 11 43 98 00 F6 15 B9 ED
<--- 69 85
Error: Failed to Mutual Authenticate!外部身份验证命令有什么问题?
注意1:我可以使用不同的Javacards (它们是SIM 02-I15)成功地进行相互身份验证,这意味着该工具正确地创建会话密钥和MAC值,但是当我想要使用我的SIM卡进行相互身份验证时,我收到了6985。
注2:基于生成的会话密钥,卡片加密是正确的。
注3:我甚至在未经修改的APDU (i=1A)上尝试了C,但是没有什么改变。
会话密钥的验证:
根据初始化更新APDU命令及其响应,我们有:
Host Challenge: 37 CD BA 7B B4 57 B5 1B
key_diversification_data : 00 00 C6 D8 6A 1C B2 02 14 13
key_info : 20 02
sequence_counter : 00 00
card_challenge : 71 90 98 C2 77 8A
card_cryptogram : 07 3D 4A 4B F1 4D D4 FB让我们用上面的数据验证生成的会话ENC密钥的正确性。基于KeyInfo数据,out SIMCard使用SCP02。在SCP02中我们有:
card_auth_data = host_challenge + sequence_counter + card_challenge + 800000000000000
==> card_auth_data = 37CDBA7BB457B51B0000719098C2778A8000000000000000
card_cryptogram = 3des_cbc_enc(card_auth_data, ZERO_IV)[-8:]
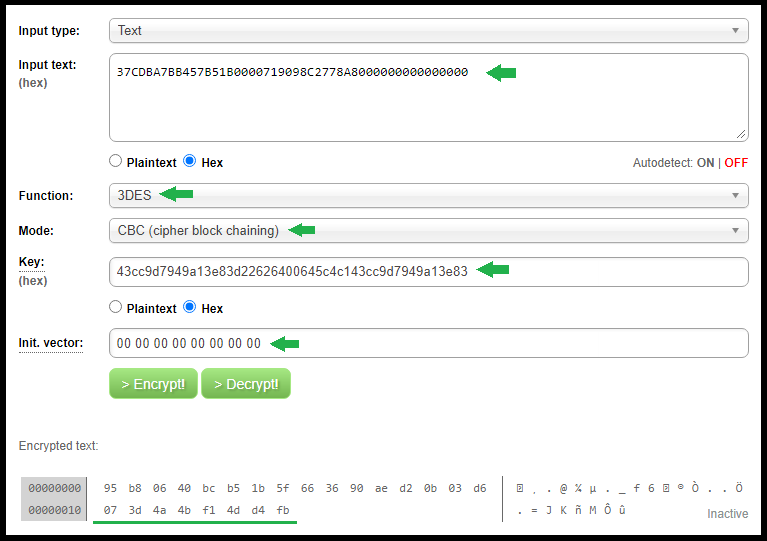
正如您在上面看到的,我们生成了与卡片在初始化更新响应中返回的值相等的卡片密码。因此会话ENC键有一个正确的值。
让我们为外部身份验证命令生成主机密码:
host_auth_data = sequence_counter + card_challenge + host_challenge + 800000000000000
==> host_auth_data = 0000719098C2778A37CDBA7BB457B51B8000000000000000
host_cryptogram = 3des_cbc_enc(host_auth_data, ZERO_IV)[-8:]
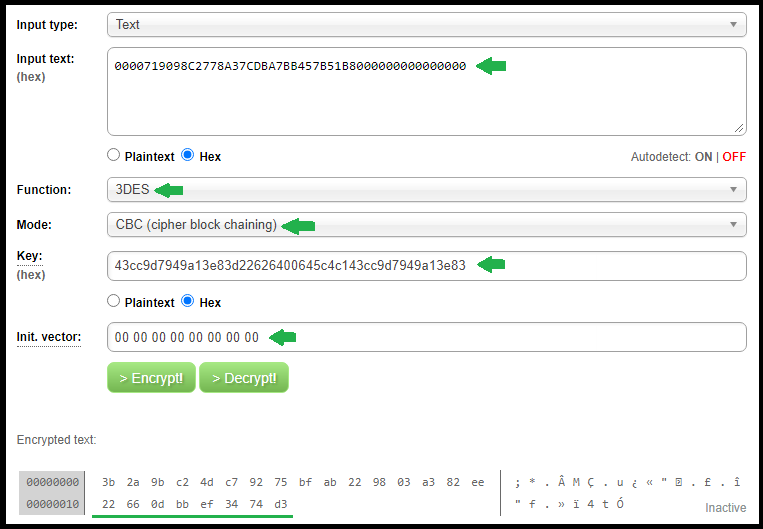
正如您在上面看到的,上面的图片中生成的host_cryptogram与我发送给卡片的值相等。
因此,我可能遇到的唯一问题是外部身份验证命令中的MAC值。假设会话密钥是正确生成的(我们不能用问题中提供的信息验证它的值,我不想公开我的卡的静态MAC密钥)。这个问题还有其他可能的原因吗?
回答 1
Stack Overflow用户
发布于 2021-07-19 20:54:17
仔细阅读你的问题时,我看到你使用的是SIM卡。
- SIM卡通常不公开SIM 02/ do 03。这样做的原因是,这些卡片不适合最终用户在读卡器中使用。SCP02 02/ is 03被禁用。对于远程更新,MNO只是在SM、BIP或CAT_TP上使用SCP80。这是不同的SCP。报告的SCP02可能是假阳性,一些SIM卡不太符合规范。
- 也是,如果您的卡可能支持SCP02,您确定有SCP02密钥吗?MNOs / SIM卡供应商在输出文件中分发,通常只有用于SCP80协议的Kic/Kid。
。
页面原文内容由Stack Overflow提供。腾讯云小微IT领域专用引擎提供翻译支持
原文链接:
https://stackoverflow.com/questions/68327163
复制相关文章
相似问题

