使用注入请求的反向工程AES密钥
使用注入请求的反向工程AES密钥
提问于 2021-11-17 00:17:04
我试图反向设计一个移动应用程序,试图获取秘密密钥,这样我就可以使用本地机器发送一个请求,尽管在这个挑战之前,我用Frida服务器解决了这个问题,但不幸的是,这一次我面临着绕过AES加密的巨大挑战。
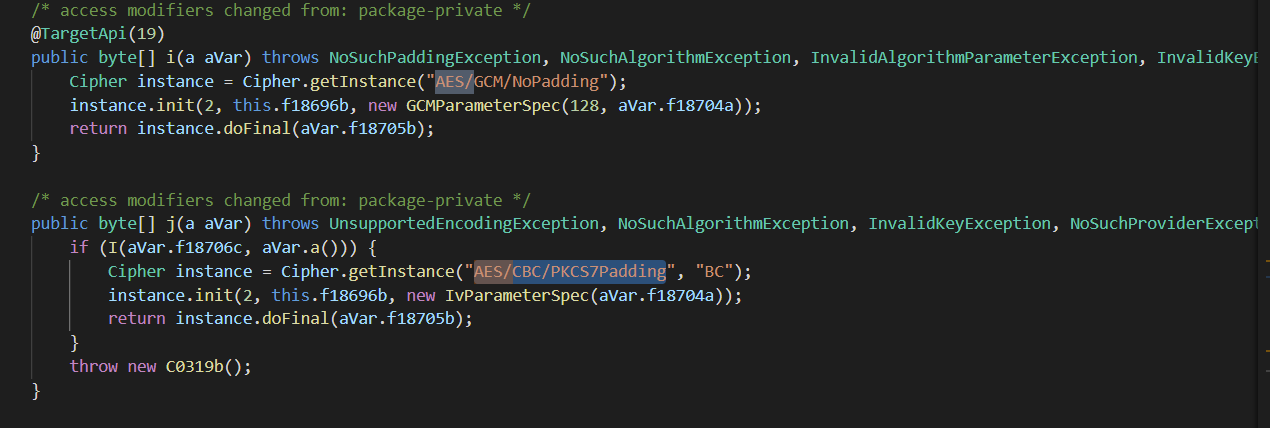
移动应用程序可以使用多种加密算法对MITM隐藏请求。因此,我对移动应用程序进行了分解,我发现使用may AES/GCM/NoPadding和AES/CBC/PKCS7Padding的应用程序是这样的代码:
package f.a.a;
import android.annotation.TargetApi;
import android.content.Context;
import android.content.SharedPreferences;
import android.os.Build;
import android.security.KeyPairGeneratorSpec;
import android.security.keystore.KeyGenParameterSpec;
import android.util.Base64;
import f.a.a.d;
import java.io.ByteArrayInputStream;
import java.io.ByteArrayOutputStream;
import java.io.IOException;
import java.io.UnsupportedEncodingException;
import java.math.BigInteger;
import java.security.GeneralSecurityException;
import java.security.InvalidAlgorithmParameterException;
import java.security.InvalidKeyException;
import java.security.KeyPairGenerator;
import java.security.KeyStore;
import java.security.KeyStoreException;
import java.security.MessageDigest;
import java.security.NoSuchAlgorithmException;
import java.security.NoSuchProviderException;
import java.security.SecureRandom;
import java.security.UnrecoverableEntryException;
import java.security.cert.CertificateException;
import java.security.interfaces.RSAPrivateKey;
import java.security.interfaces.RSAPublicKey;
import java.util.ArrayList;
import java.util.Arrays;
import java.util.Calendar;
import java.util.List;
import javax.crypto.BadPaddingException;
import javax.crypto.Cipher;
import javax.crypto.CipherInputStream;
import javax.crypto.CipherOutputStream;
import javax.crypto.IllegalBlockSizeException;
import javax.crypto.KeyGenerator;
import javax.crypto.Mac;
import javax.crypto.NoSuchPaddingException;
import javax.crypto.SecretKey;
import javax.crypto.spec.GCMParameterSpec;
import javax.crypto.spec.IvParameterSpec;
import javax.crypto.spec.SecretKeySpec;
import javax.security.auth.x500.X500Principal;
/* compiled from: EncryptionManager */
public class b {
/* renamed from: a reason: collision with root package name */
private KeyStore f18695a;
/* renamed from: b reason: collision with root package name */
private SecretKey f18696b;
/* renamed from: c reason: collision with root package name */
private SecretKey f18697c;
/* renamed from: d reason: collision with root package name */
private RSAPublicKey f18698d;
/* renamed from: e reason: collision with root package name */
private RSAPrivateKey f18699e;
/* renamed from: f reason: collision with root package name */
private boolean f18700f = false;
/* renamed from: g reason: collision with root package name */
private Context f18701g;
/* renamed from: h reason: collision with root package name */
SharedPreferences f18702h;
/* renamed from: i reason: collision with root package name */
d.c f18703i;
/* compiled from: EncryptionManager */
public static class a {
/* renamed from: a reason: collision with root package name */
byte[] f18704a = null;
/* renamed from: b reason: collision with root package name */
byte[] f18705b = null;
/* renamed from: c reason: collision with root package name */
byte[] f18706c = null;
/* access modifiers changed from: package-private */
public byte[] a() {
byte[] bArr = this.f18704a;
byte[] bArr2 = new byte[(bArr.length + this.f18705b.length)];
System.arraycopy(bArr, 0, bArr2, 0, bArr.length);
byte[] bArr3 = this.f18705b;
System.arraycopy(bArr3, 0, bArr2, this.f18704a.length, bArr3.length);
return bArr2;
}
}
/* renamed from: f.a.a.b$b reason: collision with other inner class name */
/* compiled from: EncryptionManager */
public class C0319b extends GeneralSecurityException {
public C0319b() {
super("Invalid Mac, failed to verify integrity.");
}
}
public b(Context context, SharedPreferences sharedPreferences, d.c cVar) throws IOException, NoSuchAlgorithmException, InvalidAlgorithmParameterException, NoSuchProviderException, NoSuchPaddingException, CertificateException, KeyStoreException, UnrecoverableEntryException, InvalidKeyException, IllegalStateException {
boolean z = false;
this.f18700f = sharedPreferences.getBoolean(v("sps_data_in_compat"), Build.VERSION.SDK_INT < 23);
this.f18703i = cVar;
this.f18701g = context;
this.f18702h = sharedPreferences;
B();
try {
D(context, sharedPreferences);
} catch (Exception e2) {
if (y(e2)) {
z = H(e2);
} else {
throw e2;
}
}
if (z) {
D(context, sharedPreferences);
}
}
static String E(byte[] bArr) {
StringBuilder sb = new StringBuilder();
int length = bArr.length;
for (int i2 = 0; i2 < length; i2++) {
sb.append(String.format("%02X", new Object[]{Byte.valueOf(bArr[i2])}));
}
return sb.toString();
}
public static byte[] c(String str) {
return Base64.decode(str, 2);
}
public static String d(byte[] bArr) {
return Base64.encodeToString(bArr, 2);
}
public static String v(String str) throws NoSuchAlgorithmException, UnsupportedEncodingException {
return E(MessageDigest.getInstance("SHA-256").digest(str.getBytes("UTF-8")));
}
/* access modifiers changed from: package-private */
public void A(SharedPreferences sharedPreferences) throws KeyStoreException, UnrecoverableEntryException, NoSuchAlgorithmException, NoSuchPaddingException, NoSuchProviderException, InvalidKeyException, IOException {
if (this.f18700f) {
this.f18696b = u(sharedPreferences);
this.f18697c = x(sharedPreferences);
} else if (this.f18695a.containsAlias("sps_aes_key") && this.f18695a.entryInstanceOf("sps_aes_key", KeyStore.SecretKeyEntry.class)) {
this.f18696b = ((KeyStore.SecretKeyEntry) this.f18695a.getEntry("sps_aes_key", (KeyStore.ProtectionParameter) null)).getSecretKey();
}
}
/* access modifiers changed from: package-private */
public void B() throws KeyStoreException, CertificateException, NoSuchAlgorithmException, IOException {
KeyStore instance = KeyStore.getInstance("AndroidKeyStore");
this.f18695a = instance;
instance.load((KeyStore.LoadStoreParameter) null);
}
/* access modifiers changed from: package-private */
public void C() throws KeyStoreException, UnrecoverableEntryException, NoSuchAlgorithmException {
if (this.f18695a.containsAlias("sps_rsa_key") && this.f18695a.entryInstanceOf("sps_rsa_key", KeyStore.PrivateKeyEntry.class)) {
KeyStore.PrivateKeyEntry privateKeyEntry = (KeyStore.PrivateKeyEntry) this.f18695a.getEntry("sps_rsa_key", (KeyStore.ProtectionParameter) null);
this.f18698d = (RSAPublicKey) privateKeyEntry.getCertificate().getPublicKey();
this.f18699e = (RSAPrivateKey) privateKeyEntry.getPrivateKey();
}
}
/* access modifiers changed from: package-private */
public void D(Context context, SharedPreferences sharedPreferences) throws NoSuchPaddingException, InvalidKeyException, NoSuchAlgorithmException, KeyStoreException, UnrecoverableEntryException, NoSuchProviderException, InvalidAlgorithmParameterException, IOException {
r(context, sharedPreferences);
A(sharedPreferences);
}
public byte[] F(a aVar) throws NoSuchPaddingException, InvalidAlgorithmParameterException, NoSuchAlgorithmException, KeyStoreException, UnrecoverableEntryException, NoSuchProviderException, InvalidKeyException, IOException, BadPaddingException, IllegalBlockSizeException, C0319b {
boolean z;
byte[] bArr;
try {
bArr = h(aVar);
z = false;
} catch (Exception e2) {
if (y(e2)) {
z = H(e2);
bArr = null;
} else {
throw e2;
}
}
if (!z) {
return bArr;
}
D(this.f18701g, this.f18702h);
return h(aVar);
}
public a G(byte[] bArr) throws NoSuchPaddingException, InvalidAlgorithmParameterException, NoSuchAlgorithmException, IOException, BadPaddingException, IllegalBlockSizeException, NoSuchProviderException, InvalidKeyException, KeyStoreException, UnrecoverableEntryException {
boolean z;
a aVar;
try {
aVar = l(bArr);
z = false;
} catch (Exception e2) {
if (y(e2)) {
z = H(e2);
aVar = null;
} else {
throw e2;
}
}
if (!z) {
return aVar;
}
D(this.f18701g, this.f18702h);
return l(bArr);
}
/* access modifiers changed from: package-private */
public <T extends Exception> boolean H(T t) {
d.c cVar = this.f18703i;
return cVar != null && cVar.a(t, this.f18695a, z());
}
/* access modifiers changed from: package-private */
public boolean I(byte[] bArr, byte[] bArr2) throws InvalidKeyException, NoSuchAlgorithmException {
if (bArr == null || bArr2 == null) {
return false;
}
byte[] e2 = e(bArr2);
if (e2.length != bArr.length) {
return false;
}
byte b2 = 0;
for (int i2 = 0; i2 < e2.length; i2++) {
b2 |= e2[i2] ^ bArr[i2];
}
if (b2 == 0) {
return true;
}
return false;
}
/* access modifiers changed from: package-private */
public byte[] a(byte[] bArr) throws NoSuchPaddingException, NoSuchAlgorithmException, NoSuchProviderException, InvalidKeyException, IOException {
Cipher instance = Cipher.getInstance("RSA/ECB/PKCS1Padding", "AndroidOpenSSL");
instance.init(2, this.f18699e);
CipherInputStream cipherInputStream = new CipherInputStream(new ByteArrayInputStream(bArr), instance);
ArrayList arrayList = new ArrayList();
while (true) {
int read = cipherInputStream.read();
if (read == -1) {
break;
}
arrayList.add(Byte.valueOf((byte) read));
}
int size = arrayList.size();
byte[] bArr2 = new byte[size];
for (int i2 = 0; i2 < size; i2++) {
bArr2[i2] = ((Byte) arrayList.get(i2)).byteValue();
}
cipherInputStream.close();
return bArr2;
}
/* access modifiers changed from: package-private */
public byte[] b(byte[] bArr) throws KeyStoreException, UnrecoverableEntryException, NoSuchAlgorithmException, NoSuchProviderException, NoSuchPaddingException, InvalidKeyException, IOException {
Cipher instance = Cipher.getInstance("RSA/ECB/PKCS1Padding", "AndroidOpenSSL");
instance.init(1, this.f18698d);
ByteArrayOutputStream byteArrayOutputStream = new ByteArrayOutputStream();
CipherOutputStream cipherOutputStream = new CipherOutputStream(byteArrayOutputStream, instance);
cipherOutputStream.write(bArr);
cipherOutputStream.close();
return byteArrayOutputStream.toByteArray();
}
/* access modifiers changed from: package-private */
public byte[] e(byte[] bArr) throws NoSuchAlgorithmException, InvalidKeyException {
Mac instance = Mac.getInstance("HmacSHA256");
instance.init(this.f18697c);
return instance.doFinal(bArr);
}
/* access modifiers changed from: package-private */
public a f(String str) {
a aVar = new a();
String[] split = str.split("]");
aVar.f18704a = c(split[0]);
aVar.f18705b = c(split[1]);
if (split.length > 2) {
aVar.f18706c = c(split[2]);
}
return aVar;
}
/* access modifiers changed from: package-private */
public String g(String str) throws IOException, NoSuchPaddingException, InvalidKeyException, NoSuchAlgorithmException, IllegalBlockSizeException, BadPaddingException, C0319b, NoSuchProviderException, InvalidAlgorithmParameterException, KeyStoreException, UnrecoverableEntryException {
if (str == null || str.length() <= 0) {
return null;
}
byte[] F = F(f(str));
return new String(F, 0, F.length, "UTF-8");
}
public byte[] h(a aVar) throws IOException, NoSuchPaddingException, InvalidAlgorithmParameterException, NoSuchAlgorithmException, IllegalBlockSizeException, BadPaddingException, C0319b, NoSuchProviderException, InvalidKeyException {
if (aVar == null || aVar.f18705b == null) {
return null;
}
if (this.f18700f) {
return j(aVar);
}
return i(aVar);
}
/* access modifiers changed from: package-private */
@TargetApi(19)
public byte[] i(a aVar) throws NoSuchPaddingException, NoSuchAlgorithmException, InvalidAlgorithmParameterException, InvalidKeyException, BadPaddingException, IllegalBlockSizeException, UnsupportedEncodingException {
Cipher instance = Cipher.getInstance("AES/GCM/NoPadding");
instance.init(2, this.f18696b, new GCMParameterSpec(128, aVar.f18704a));
return instance.doFinal(aVar.f18705b);
}
/* access modifiers changed from: package-private */
public byte[] j(a aVar) throws UnsupportedEncodingException, NoSuchAlgorithmException, InvalidKeyException, NoSuchProviderException, NoSuchPaddingException, InvalidAlgorithmParameterException, BadPaddingException, IllegalBlockSizeException, C0319b {
if (I(aVar.f18706c, aVar.a())) {
Cipher instance = Cipher.getInstance("AES/CBC/PKCS7Padding", "BC");
instance.init(2, this.f18696b, new IvParameterSpec(aVar.f18704a));
return instance.doFinal(aVar.f18705b);
}
throw new C0319b();
}
/* access modifiers changed from: package-private */
public String k(a aVar) {
if (aVar.f18706c != null) {
return d(aVar.f18704a) + "]" + d(aVar.f18705b) + "]" + d(aVar.f18706c);
}
return d(aVar.f18704a) + "]" + d(aVar.f18705b);
}
public a l(byte[] bArr) throws NoSuchPaddingException, NoSuchAlgorithmException, InvalidKeyException, IOException, BadPaddingException, NoSuchProviderException, IllegalBlockSizeException, InvalidAlgorithmParameterException {
if (bArr == null || bArr.length <= 0) {
return null;
}
byte[] w = w();
if (this.f18700f) {
return o(bArr, w);
}
return n(bArr, w);
}
/* access modifiers changed from: package-private */
public String m(String str) throws InvalidKeyException, NoSuchAlgorithmException, NoSuchPaddingException, IOException, IllegalBlockSizeException, InvalidAlgorithmParameterException, NoSuchProviderException, BadPaddingException, KeyStoreException, UnrecoverableEntryException {
if (str == null || str.length() <= 0) {
return null;
}
return k(G(str.getBytes("UTF-8")));
}
/* access modifiers changed from: package-private */
@TargetApi(19)
public a n(byte[] bArr, byte[] bArr2) throws NoSuchPaddingException, NoSuchAlgorithmException, InvalidAlgorithmParameterException, InvalidKeyException, BadPaddingException, IllegalBlockSizeException, UnsupportedEncodingException {
Cipher instance = Cipher.getInstance("AES/GCM/NoPadding");
instance.init(1, this.f18696b, new GCMParameterSpec(128, bArr2));
a aVar = new a();
aVar.f18704a = instance.getIV();
aVar.f18705b = instance.doFinal(bArr);
return aVar;
}
/* access modifiers changed from: package-private */
public a o(byte[] bArr, byte[] bArr2) throws NoSuchPaddingException, NoSuchAlgorithmException, NoSuchProviderException, InvalidKeyException, BadPaddingException, IllegalBlockSizeException, UnsupportedEncodingException, InvalidAlgorithmParameterException {
Cipher instance = Cipher.getInstance("AES/CBC/PKCS7Padding", "BC");
instance.init(1, this.f18696b, new IvParameterSpec(bArr2));
a aVar = new a();
aVar.f18704a = instance.getIV();
aVar.f18705b = instance.doFinal(bArr);
aVar.f18706c = e(aVar.a());
return aVar;
}
/* access modifiers changed from: package-private */
@TargetApi(23)
public boolean p() throws KeyStoreException, NoSuchProviderException, NoSuchAlgorithmException, InvalidAlgorithmParameterException {
Calendar instance = Calendar.getInstance();
Calendar instance2 = Calendar.getInstance();
instance2.add(1, 25);
if (this.f18695a.containsAlias("sps_aes_key")) {
return false;
}
KeyGenerator instance3 = KeyGenerator.getInstance("AES", "AndroidKeyStore");
instance3.init(new KeyGenParameterSpec.Builder("sps_aes_key", 3).setCertificateSubject(new X500Principal("CN = Secured Preference Store, O = Devliving Online")).setCertificateSerialNumber(BigInteger.ONE).setKeySize(256).setKeyValidityEnd(instance2.getTime()).setKeyValidityStart(instance.getTime()).setBlockModes(new String[]{"GCM"}).setEncryptionPaddings(new String[]{"NoPadding"}).setRandomizedEncryptionRequired(false).build());
instance3.generateKey();
return true;
}
/* access modifiers changed from: package-private */
public boolean q(SharedPreferences sharedPreferences) throws IOException, NoSuchAlgorithmException, NoSuchPaddingException, InvalidKeyException, KeyStoreException, NoSuchProviderException, UnrecoverableEntryException {
String v = v("sps_aes_key");
if (sharedPreferences.contains(v)) {
return false;
}
KeyGenerator instance = KeyGenerator.getInstance("AES");
instance.init(256);
boolean commit = sharedPreferences.edit().putString(v, d(b(instance.generateKey().getEncoded()))).commit();
sharedPreferences.edit().putBoolean(v("sps_data_in_compat"), true).apply();
return commit;
}
/* access modifiers changed from: package-private */
public void r(Context context, SharedPreferences sharedPreferences) throws KeyStoreException, NoSuchProviderException, NoSuchAlgorithmException, InvalidAlgorithmParameterException, UnrecoverableEntryException, NoSuchPaddingException, InvalidKeyException, IOException {
if (!this.f18700f) {
p();
return;
}
t(context);
C();
q(sharedPreferences);
s(sharedPreferences);
}
/* access modifiers changed from: package-private */
public boolean s(SharedPreferences sharedPreferences) throws NoSuchPaddingException, InvalidKeyException, NoSuchAlgorithmException, KeyStoreException, NoSuchProviderException, UnrecoverableEntryException, IOException {
String v = v("sps_mac_key");
if (sharedPreferences.contains(v)) {
return false;
}
byte[] bArr = new byte[32];
new SecureRandom().nextBytes(bArr);
return sharedPreferences.edit().putString(v, d(b(bArr))).commit();
}
/* access modifiers changed from: package-private */
public void t(Context context) throws NoSuchProviderException, NoSuchAlgorithmException, InvalidAlgorithmParameterException, KeyStoreException {
KeyPairGeneratorSpec keyPairGeneratorSpec;
if (!this.f18695a.containsAlias("sps_rsa_key")) {
Calendar instance = Calendar.getInstance();
Calendar instance2 = Calendar.getInstance();
instance2.add(1, 25);
KeyPairGenerator instance3 = KeyPairGenerator.getInstance("RSA", "AndroidKeyStore");
if (Build.VERSION.SDK_INT >= 19) {
keyPairGeneratorSpec = new KeyPairGeneratorSpec.Builder(context).setAlias("sps_rsa_key").setKeySize(2048).setKeyType("RSA").setEndDate(instance2.getTime()).setStartDate(instance.getTime()).setSerialNumber(BigInteger.ONE).setSubject(new X500Principal("CN = Secured Preference Store, O = Devliving Online")).build();
} else {
keyPairGeneratorSpec = new KeyPairGeneratorSpec.Builder(context).setAlias("sps_rsa_key").setEndDate(instance2.getTime()).setStartDate(instance.getTime()).setSerialNumber(BigInteger.ONE).setSubject(new X500Principal("CN = Secured Preference Store, O = Devliving Online")).build();
}
instance3.initialize(keyPairGeneratorSpec);
instance3.generateKeyPair();
}
}
/* access modifiers changed from: package-private */
public SecretKey u(SharedPreferences sharedPreferences) throws IOException, NoSuchAlgorithmException, InvalidKeyException, NoSuchProviderException, NoSuchPaddingException {
String string = sharedPreferences.getString(v("sps_aes_key"), (String) null);
if (string != null) {
return new SecretKeySpec(a(c(string)), "AES");
}
return null;
}
/* access modifiers changed from: package-private */
public byte[] w() throws UnsupportedEncodingException {
byte[] bArr = !this.f18700f ? new byte[12] : new byte[16];
new SecureRandom().nextBytes(bArr);
return bArr;
}
/* access modifiers changed from: package-private */
public SecretKey x(SharedPreferences sharedPreferences) throws IOException, NoSuchAlgorithmException, InvalidKeyException, NoSuchProviderException, NoSuchPaddingException {
String string = sharedPreferences.getString(v("sps_mac_key"), (String) null);
if (string != null) {
return new SecretKeySpec(a(c(string)), "HmacSHA256");
}
return null;
}
/* access modifiers changed from: package-private */
public <T extends Exception> boolean y(T t) {
return (t instanceof KeyStoreException) || (t instanceof UnrecoverableEntryException) || (t instanceof InvalidKeyException) || (t instanceof IllegalStateException) || ((t instanceof IOException) && t.getCause() != null && (t.getCause() instanceof BadPaddingException));
}
/* access modifiers changed from: package-private */
public List<String> z() {
return Arrays.asList(new String[]{"sps_aes_key", "sps_rsa_key"});
}
}这是请求的一个示例。
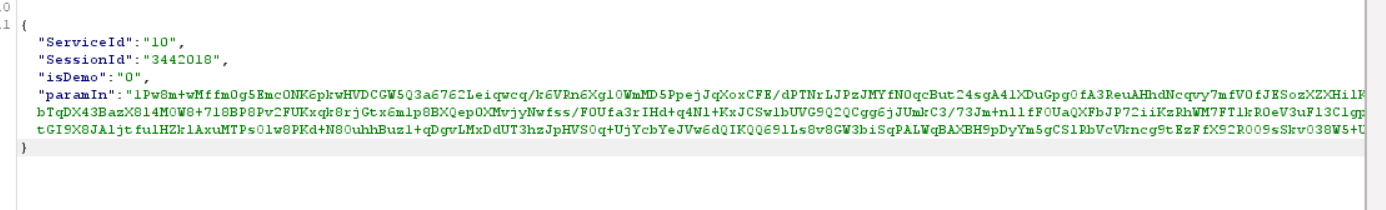
这是解压缩密码
我尝试使用一个JS代码使用Frida注入移动应用程序
console.log("Script loaded");
Java.perform(function x() {
//hooking SecretKeySpec's constructor to get the SecretKeySpec
var secret_key_spec = Java.use("javax.crypto.spec.SecretKeySpec");
secret_key_spec.$init.overload("[B", "java.lang.String").implementation = function (x, y) {
//send('{"my_type" : "KEY"}', new Uint8Array(x));
console.log(Uint8Array(x));
}
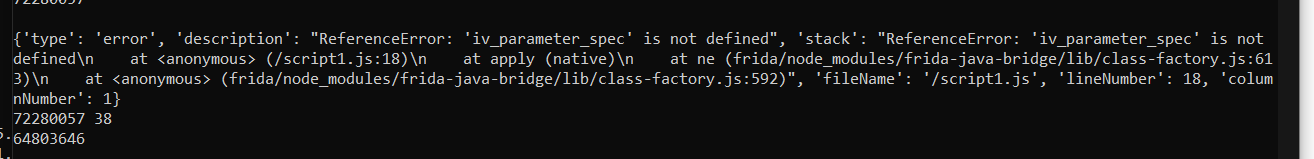
});但我总是会犯错误:
然后我想到了一个可能是我错了的想法,我想用一个带有有效载荷密钥的POST请求注入加密JAVA文件到我的Web钩子,然后重新编译移动应用程序,然后推到我的设备机器上,测试我是否能接收到请求,这样我就可以在那里找到秘密密钥了。
如果有人在逆向工程师方面有很大的知识可以帮助!或者,如果有任何机会,这是可以解决的,这将是超级惊人的!
谢谢<3
回答 1
Stack Overflow用户
发布于 2022-11-08 00:12:28
我犯了同样的错误
- 安装最少版本的python版本和pip3
使用以下方法安装
pip3 install frida
- 安装frida工具
sudo pip3 install frida-tools
您可以这样看,您必须使用sudo来避免错误。
工作代码示例(如果需要 )
页面原文内容由Stack Overflow提供。腾讯云小微IT领域专用引擎提供翻译支持
原文链接:
https://stackoverflow.com/questions/69997558
复制相关文章
相似问题

