如何正确传递预提交args,使terraform checkov预提交钩子的输出更少冗长?
如何正确传递预提交args,使terraform checkov预提交钩子的输出更少冗长?
提问于 2022-11-09 16:45:41
虽然我发现切可夫是一个很好的工具,但是默认的输出过于冗长:
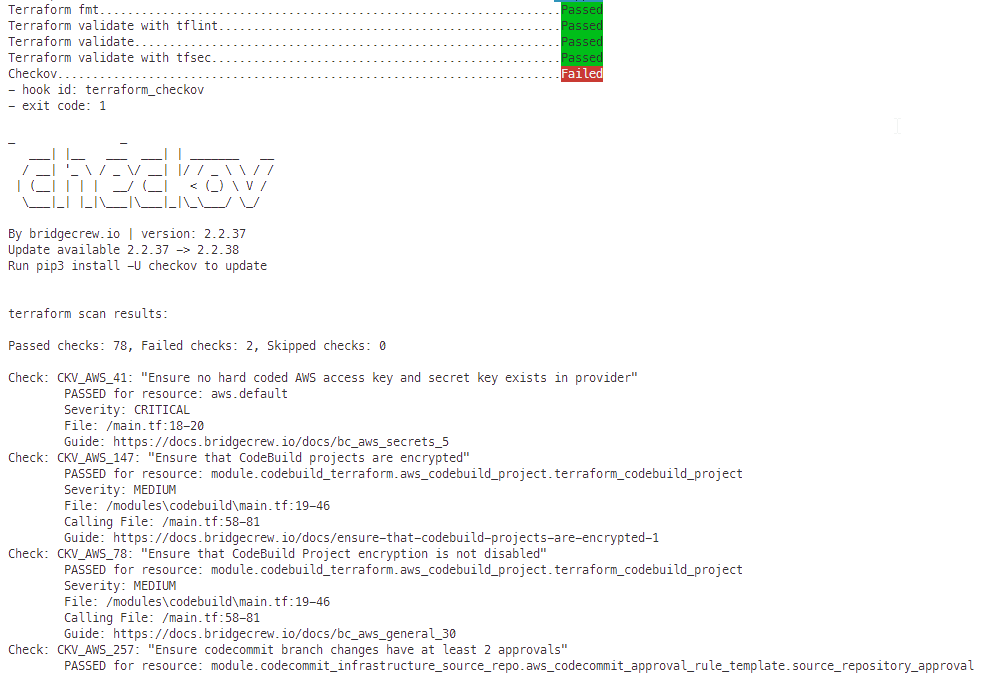
在我的上面的例子中,它转储了终端输出中的所有78次通过检查,这使得很难找到需要修复的实际错误。事实上,输出是如此冗长,以至于它开始切断许多以前的输出,而我实际上仍然需要看到这些输出。
在我的预承诺设置中,我将此检查作为许多terraform检查工具之一嵌入,如下所示:
- repo: https://github.com/antonbabenko/pre-commit-terraform
rev: v1.76.0
hooks:
- id: terraform_checkov
- ...过滤checkov --help输出的关键字,如“详细”或"CLI",我发现这两个标志:
❯ checkov --help | grep CLI
--quiet in case of CLI output, display only failed checks.
--compact in case of CLI output, do not display code blocks为了解决我的问题,我将这两种方法都添加到预提交钩子的args-部分:
- id: terraform_checkov
args: ["--quiet", "--compact"]然而,运行预提交钩子失败:
❯ git add -A && pre-commit run terraform_checkov
Checkov..................................................................Failed step
- hook id: terraform_checkov
- exit code: 1
getopt: unrecognized option '--quiet'
getopt: unrecognized option '--compact'因此,我仍然在寻找一种确切的可能性,特别是平面--quiet应该做什么:
我只想在终端输出中看到出了什么问题,而不想看到什么是正确的。
回答 1
Stack Overflow用户
回答已采纳
发布于 2022-11-09 17:20:11
最后,我在通用terraform相关预提交页面上找到了一个示例,可以用它相应地编辑“.accordingly config.yaml”文件:
...
- id: terraform_checkov
args:
- --args=--quiet
- --args=--compact
...有了这种传递论点的特殊方式,它现在起作用了。
尽管如此,的可能更少,因为在相同的terraform代码位置上的2次失败检查将转换为以下输出:
Checkov........................................................................Failed
- hook id: terraform_checkov
- exit code: 1
terraform scan results:
Passed checks: 78, Failed checks: 2, Skipped checks: 0
Check: CKV_AWS_109: "Ensure IAM policies does not allow permissions management / resource exposure without constraints"
FAILED for resource: module.codepipeline_kms.aws_iam_policy_document.kms_key_policy_doc
Severity: LOW
File: /modules\kms\main.tf:31-101
Calling File: /main.tf:83-93
Guide: https://docs.bridgecrew.io/docs/ensure-iam-policies-do-not-allow-permissions-management-resource-exposure-without-constraint
Check: CKV_AWS_111: "Ensure IAM policies does not allow write access without constraints"
FAILED for resource: module.codepipeline_kms.aws_iam_policy_document.kms_key_policy_doc
Severity: LOW
File: /modules\kms\main.tf:31-101
Calling File: /main.tf:83-93
Guide: https://docs.bridgecrew.io/docs/ensure-iam-policies-do-not-allow-write-access-without-constraint
More details: https://www.bridgecrew.cloud/projects?repository=oauto_cli_repo/infrastructure&branch=bc-94b0d20_master&runId=latest
More details: https://www.bridgecrew.cloud/projects?repository=oauto_cli_repo/codebuild&branch=bc-414954b_master&runId=latest
terraform scan results:
Passed checks: 2, Failed checks: 0, Skipped checks: 0
More details: https://www.bridgecrew.cloud/projects?repository=oauto_cli_repo/codecommit&branch=bc-b61d2e2_master&runId=latest
terraform scan results:
Passed checks: 1, Failed checks: 0, Skipped checks: 0
More details: https://www.bridgecrew.cloud/projects?repository=oauto_cli_repo/codepipeline&branch=bc-85a3952_master&runId=latest
terraform scan results:
Passed checks: 7, Failed checks: 0, Skipped checks: 0
More details: https://www.bridgecrew.cloud/projects?repository=oauto_cli_repo/iam-role&branch=bc-73bb537_master&runId=latest
terraform scan results:
Passed checks: 9, Failed checks: 2, Skipped checks: 0
Check: CKV_AWS_109: "Ensure IAM policies does not allow permissions management / resource exposure without constraints"
FAILED for resource: aws_iam_policy_document.kms_key_policy_doc
Severity: LOW
File: /main.tf:31-101
Guide: https://docs.bridgecrew.io/docs/ensure-iam-policies-do-not-allow-permissions-management-resource-exposure-without-constraint
Check: CKV_AWS_111: "Ensure IAM policies does not allow write access without constraints"
FAILED for resource: aws_iam_policy_document.kms_key_policy_doc
Severity: LOW
File: /main.tf:31-101
Guide: https://docs.bridgecrew.io/docs/ensure-iam-policies-do-not-allow-write-access-without-constraint
More details: https://www.bridgecrew.cloud/projects?repository=oauto_cli_repo/kms&branch=bc-17050bc_master&runId=latest
terraform scan results:
Passed checks: 56, Failed checks: 0, Skipped checks: 0
More details: https://www.bridgecrew.cloud/projects?repository=oauto_cli_repo/s3&branch=bc-125b61a_master&runId=latest选择的编辑:
正如@James Woolfenden在我的OP下面的第一个评论中所指出的
Anton的钩子不是checkov官方支持的: github.com/bridgecrewio/checkov
页面原文内容由Stack Overflow提供。腾讯云小微IT领域专用引擎提供翻译支持
原文链接:
https://stackoverflow.com/questions/74378473
复制相关文章
相似问题

