无法激活PIM角色
无法激活PIM角色
提问于 2022-10-21 07:08:42
堆栈过流
我试图激活powershell中的角色分配。基本上,我尝试创建一个脚本,只需一次单击就可以运行我的所有角色--而不是我需要访问AzureAD并单击每个角色并激活它们。(然后等待激活)。
所以基本上我试过这个:
$schedule = New-Object Microsoft.Open.MSGraph.Model.AzureADMSPrivilegedSchedule
$schedule.Type = "Once"
#Schedule starts from now
$schedule.StartDateTime =(Get-Date).ToUniversalTime().ToString("yyyy-MM-ddTHH:mm:ss.fffZ")
#Schedule ends after 4 hours
$schedule.endDateTime = (Get-Date).AddHours(0.5).ToUniversalTime().ToString("yyyy-MM-ddTHH:mm:ss.fffZ")
Open-AzureADMSPrivilegedRoleAssignmentRequest -ProviderId 'aadRoles'
-ResourceId '<My Resource ID>' -RoleDefinitionId 'fe930be7-5e62-47db-91af-98c3a49a38b1' -SubjectId 'af25fdae-dc28-4855-b22d-4f5881b89ea9' -AssignmentState 'Active' -Type 'userAdd' -Schedule $schedule -Reason "Work"我收到的错误:
Open-AzureADMSPrivilegedRoleAssignmentRequest : Error occurred while executing
OpenAzureADMSPrivilegedRoleAssignmentRequest
Code: InvalidScope
Message: The resource scope is not valid.
InnerError:
RequestId: 766f029f-0be6-420b-b961-f56ce8736bd6
DateTimeStamp: Fri, 21 Oct 2022 06:36:21 GMT
HttpStatusCode: BadRequest
HttpStatusDescription: Bad Request
HttpResponseStatus: Completed
At line:10 char:1
+ Open-AzureADMSPrivilegedRoleAssignmentRequest -ProviderId 'aadRoles' ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : NotSpecified: (:) [Open-AzureADMSP...signmentRequest], ApiException
+ FullyQualifiedErrorId : Microsoft.Open.MSGraphBeta.Client.ApiException,Microsoft.Open.MSGraphBeta.PowerShell.OpenAzureADMSPrivilegedRoleAssignmentRequest当我试图将-Type "userAdd“更改为-Type "adminAdd”时,错误是不同的:
Open-AzureADMSPrivilegedRoleAssignmentRequest : Error occurred while executing
OpenAzureADMSPrivilegedRoleAssignmentRequest
Code: RoleAssignmentRequestPolicyValidationFailed
Message: The following policy rules failed: ["AdminRequestRule"]
InnerError:
RequestId: f180bba3-d557-491f-b4be-525b8a0d6483
DateTimeStamp: Fri, 21 Oct 2022 06:55:01 GMT
HttpStatusCode: BadRequest
HttpStatusDescription: Bad Request
HttpResponseStatus: Completed
At line:7 char:1
+ Open-AzureADMSPrivilegedRoleAssignmentRequest -ProviderId 'aadRoles' ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : NotSpecified: (:) [Open-AzureADMSP...signmentRequest], ApiException
+ FullyQualifiedErrorId : Microsoft.Open.MSGraphBeta.Client.ApiException,Microsoft.Open.MSGraphBeta.PowerShell.OpenAzureADMSPrivilegedRoleAssignmentRequest其实我是找不到解决办法的。也许是角色的一些设置?我也尝试将-AssigmentState更改为“合格”,但变化不大。
回答 2
Stack Overflow用户
发布于 2022-10-21 09:48:41
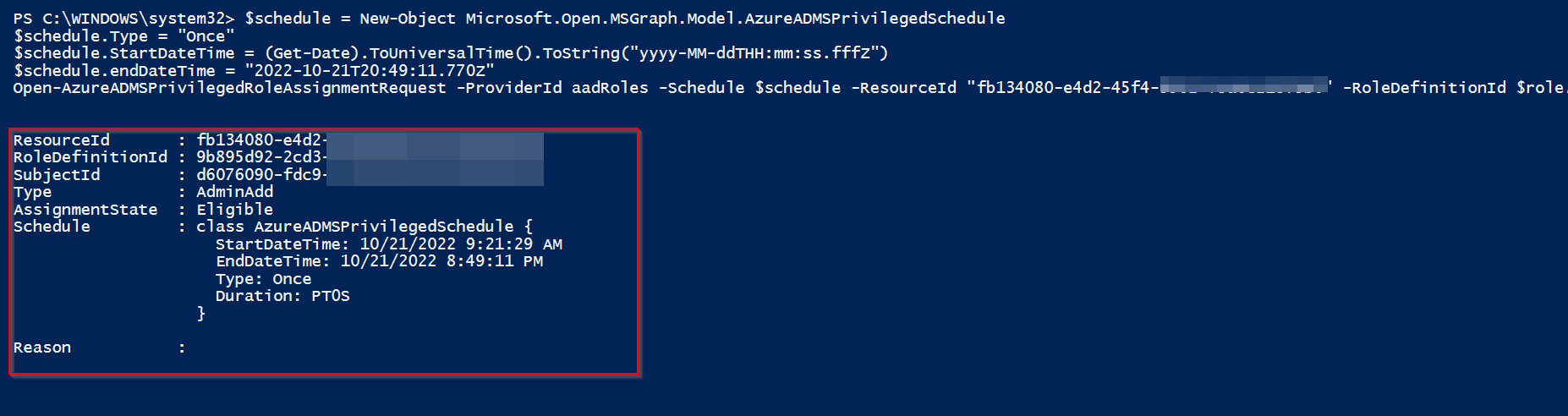
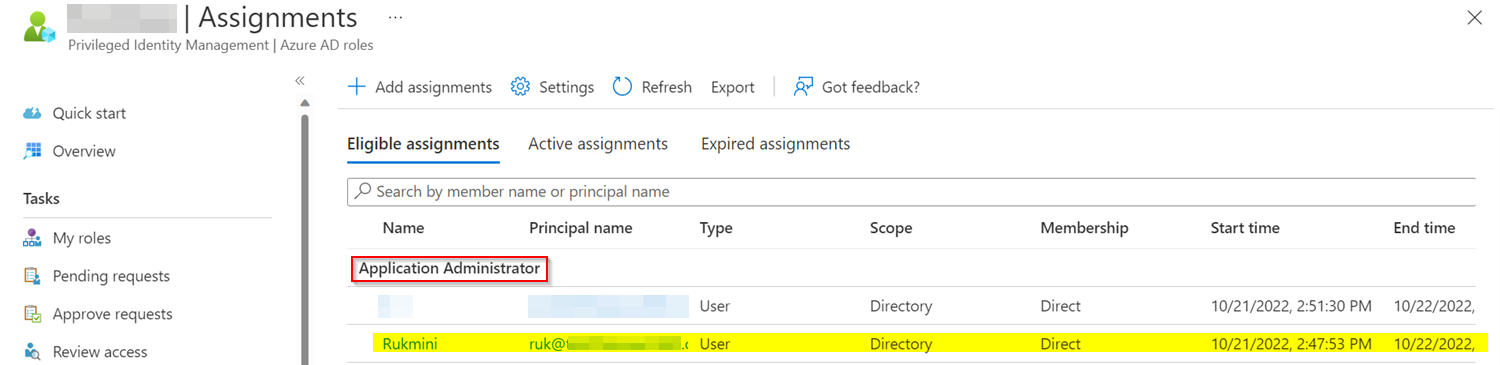
我尝试在我的环境中复制相同的结果,得到的结果与下面的相同
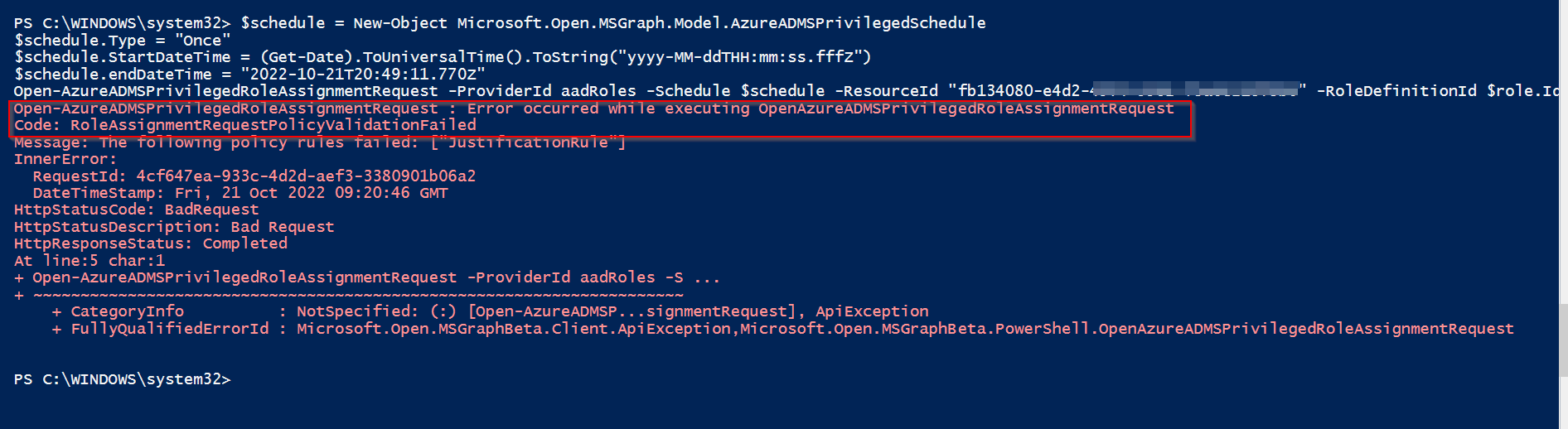
要解决错误,请尝试使用以下PowerShell脚本:
$role = Get-AzureADMSPrivilegedRoleDefinition -ProviderId aadRoles -ResourceId "TenantId" | Where-Object {$_.DisplayName -eq 'Application Administrator'}
$schedule = New-Object Microsoft.Open.MSGraph.Model.AzureADMSPrivilegedSchedule
$schedule.Type = "Once"
$schedule.StartDateTime = (Get-Date).ToUniversalTime().ToString("yyyy-MM-ddTHH:mm:ss.fffZ")
$schedule.endDateTime = "2022-10-21T20:49:11.770Z"
Open-AzureADMSPrivilegedRoleAssignmentRequest -ProviderId aadRoles -Schedule $schedule -ResourceId "TenantId" -RoleDefinitionId $role.Id -SubjectId "UserObjectId" -AssignmentState "Eligible" -Type "AdminAdd"
Stack Overflow用户
发布于 2022-10-21 13:17:11
因为我遇到了同样的问题,我在搜索中找到了你的帖子。目前,我相信,AzureAD预览模块根本不支持激活合格的,但范围内的分配。
以下是我在网上发现的:
和
https://github.com/Azure/azure-powershell/issues/16476
后者是一个特性请求,它是关于创建一个作用域赋值,而不是激活它,但我担心效果是一样的:不支持范围赋值(目前)。悲观的回答是,人们应该将这一请求提交给MS支持部门。
--
干杯,
主键
页面原文内容由Stack Overflow提供。腾讯云小微IT领域专用引擎提供翻译支持
原文链接:
https://stackoverflow.com/questions/74149941
复制相关文章
相似问题

